App-roval: The best and worst apps for user privacy and safety



- ExpressVPN’s “App-roval” report evaluates the top apps for user safety based on criteria like app store ratings, data breach history, in-app purchases, security features, and privacy policies. It’s aimed to guide users toward safer app choices.
.
- DuckDuckGo, Signal, and ProtonMail are the top-rated for privacy and security. DuckDuckGo offers features like tracker blocking and a privacy-focused search engine, while Signal and ProtonMail provide secure communication with end-to-end encryption and minimal data collection.
.
- Free gaming apps, including Race Master 3D and Subway Surfers, lack key security features like 2FA and strong password protection, posing risks to user data.
.
- YouTube, TikTok, and Roblox have been criticized for inadequate privacy practices, such as unclear data usage policies, which potentially compromise user privacy.
.
- Utilizing a VPN can improve safety by encrypting data and protecting against eavesdropping. However, choosing apps with robust security features is essential for optimal privacy and safety.
Have you ever had a conversation with your friends about a particular product, only to see it pop up as an ad on social media soon after? Or noticed an app accessing your photos or tracking your location without asking for your permission first? If you’ve answered “yes” to any of these, then you’re not alone. These experiences raise important questions about app privacy and user data security.
With these concerns in mind, ExpressVPN conducted the “App-roval” report, diving deep into the mobile app ecosystem. We scrutinized a broad range of apps across various categories, including social media, entertainment, sports, gaming, food, shopping, and travel.
Our methodology focused on evaluating privacy and security factors such as app store ratings, history of data breaches, availability of in-app purchases, security measures (encryption, two-factor authentication), password protection, and privacy policies. Each app was assessed and scored on these criteria, resulting in an overall safety rating out of 100%, to inform you which apps are the most secure and privacy-conscious.
Let’s dive into our findings.
Jump to...
The most secure apps
Best apps for user privacy
The best app for security and privacy
Why gaming apps are problematic
Privacy concerns in popular apps
Methodology
Unveiling 2024’s most secure mobile apps
With a major study finding that a cyber attack occurs every 39 seconds, affecting one in three Americans each year, the importance of robust app security can’t be overstated. When it comes to an app’s security measures, three key features are considered the baseline requirement: Password protection (requiring a secure password as well as offering password use for certain parts of the app), two-factor authentication, and a strong encryption standard appropriate for the app’s use. These elements are essential for securing user data against unauthorized access.
To analyze the most secure apps on the market, we measured them against these security features and also considered additional safety measures they implement, to discover which brands take user safety seriously.
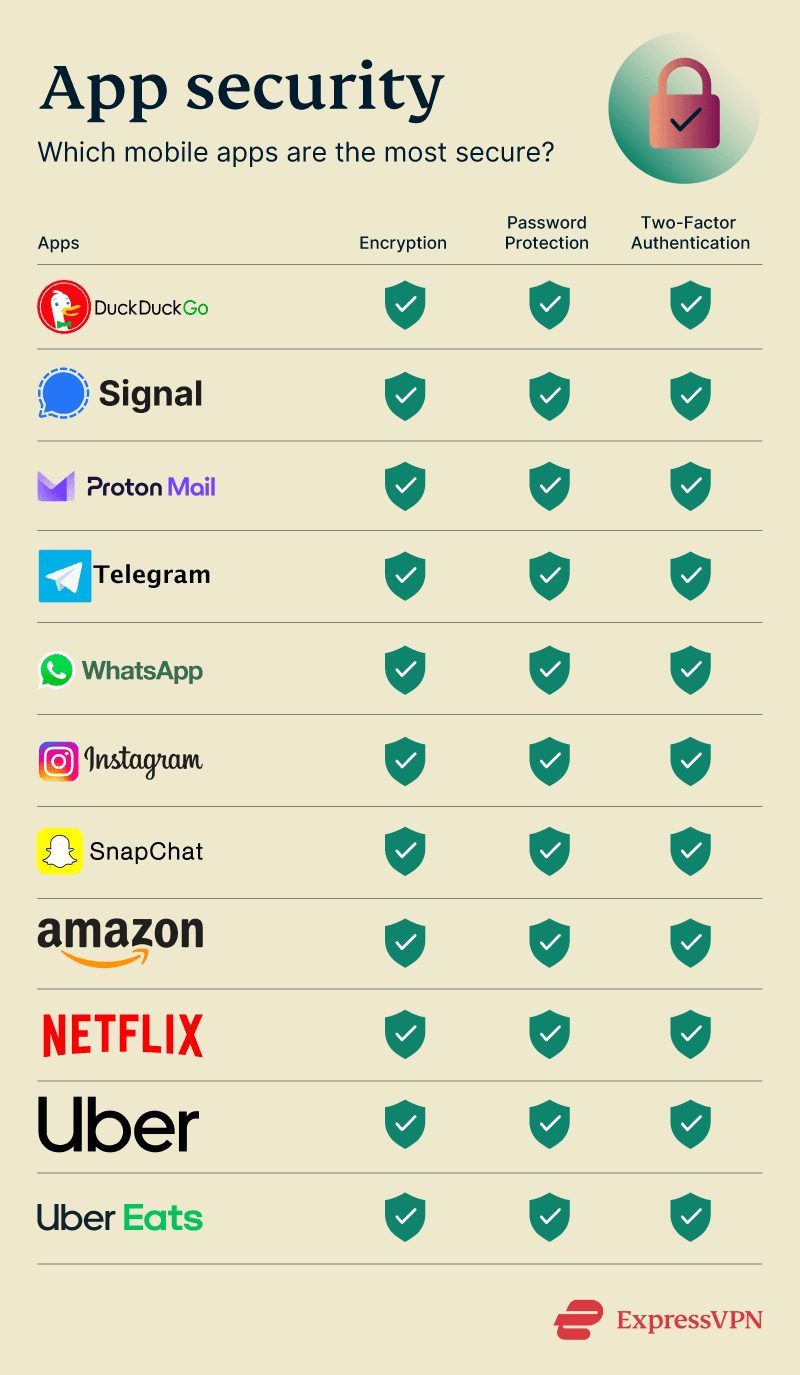
Best apps for security overall
DuckDuckGo
DuckDuckGo’s browser app that incorporates its search engine stands out as a leader in online privacy and security, with an impressive overall safety rating of 95%. Its commitment to user privacy is evident through a range of features designed to enhance security and ensure anonymity while browsing.
- Tracker radar: DuckDuckGo identifies and blocks trackers from websites, preventing them from collecting your data as you browse. This feature is part of its broader effort to limit the amount of information websites can gather about users.
- Burn Bar: A standout feature in the DuckDuckGo app, the Burn Bar allows users to instantly delete all browsing data with a single tap on the fire icon. This ensures that your search history and site data are not stored, maintaining a high level of privacy.
- Global Privacy Control (GPC): DuckDuckGo supports GPC, an opt-in standard that signals to websites your desire to have your browsing privacy respected. Websites compliant with GPC will only retain the minimum amount of information necessary from your interactions.
- Privacy grade ratings: DuckDuckGo evaluates websites based on the number of tracking requests blocked and their terms of service agreements. It then assigns a privacy grade to help users understand the privacy practices of the sites they visit.
- Email protection: DuckDuckGo offers an email protection feature that strips tracking devices from emails before they reach you. This is done through a "Duck address," which forwards cleaned emails to your actual email account without revealing personal information.
- Content Security Policy (CSP): CSP helps protect users from malicious websites by blocking third-party websites that may launch cyberattacks. This feature guards against various online threats, including XSS attacks, code injection, and clickjacking.
- Blocking embedded social media content: DuckDuckGo prevents social media platforms from tracking users through embedded content on websites. This limits the data collected by social media sites when you view embedded posts or videos.
- Search leakage prevention: DuckDuckGo ensures that your clicks on search results do not leak data to third-party websites. It uses encryption and reroutes clicks to prevent websites from identifying how you arrived at their site.
- No user profile collection: Unlike other search engines that build a user profile based on your searches and browsing history, DuckDuckGo doesn’t collect or store personal data. This means you can search without personalized ads or filter bubbles.
- Tor exit enclave: For users seeking additional anonymity, DuckDuckGo operates a Tor exit enclave. This allows for fully encrypted internet activity through Tor, adding another layer of privacy to your browsing experience.
Signal
Privacy-focused chat app Signal is highly regarded for its focus on security and privacy, achieving an impressive overall safety rating of 87%. Here's a detailed look at some of Signal's standout security features that reinforce its position as a leading app for user safety:
- End-to-end encryption: All communications on Signal, including messages, calls, and media, are secured with end-to-end encryption, ensuring that only the communicating users can access the content of their conversations.
- Safety numbers: This unique feature allows users to verify the security of their conversations by comparing safety numbers with the person they're communicating with. This helps ensure you're connected to the intended recipient and prevents man-in-the-middle attacks.
- Minimal data collection: Signal's privacy policy is notable for the minimal amount of data it collects. Apart from phone numbers, random keys, and minimal profile information, Signal does not store any metadata that could be used to identify the content of communications or the participants in a conversation. This commitment to privacy was highlighted when Signal was unable to provide user data in response to a subpoena, as the data requested does not exist on its servers.
- Disappearing messages: Users can set messages to automatically disappear after a set period, enhancing privacy and ensuring sensitive information does not remain accessible indefinitely.
- Screen security: Signal offers features to block screenshots within the app, adding an additional layer of privacy for users. This prevents sensitive information from being captured and shared without consent.
- Sealed sender: This feature adds an extra layer of privacy by hiding the sender's identity from Signal servers, making it impossible for Signal to know who is messaging whom.
- Open source: Signal's code is open source, allowing for independent verification of its security and privacy features by experts worldwide. This transparency builds trust and ensures any vulnerabilities are quickly identified and addressed.
ProtonMail
ProtonMail, recognized for its strong commitment to privacy and security, offers a comprehensive suite of features that contribute to its 70% overall safety rating.
- End-to-end and zero-access encryption: ProtonMail ensures that your emails are encrypted at all times, making it impossible for anyone, including ProtonMail's own staff, to access the content of your emails. This level of encryption is automatic and requires no special software or technical skills from the user.
- Password-protected emails: This feature allows you to send encrypted emails to any recipient, regardless of whether they use ProtonMail. By setting a password for the email, you ensure that only the intended recipient can open it, enhancing security for sensitive communications.
- Proton sentinel: A sophisticated security system, Proton Sentinel monitors accounts for signs of infiltration or takeover attempts. It combines artificial intelligence with the expertise of security analysts to provide a high level of protection, especially for users at a greater risk of attacks.
- 2FA with hardware security keys: ProtonMail supports 2FA using hardware security keys like YubiKey, offering a physical layer of security that is difficult for online attackers to bypass.
- Enhanced tracking protection: To protect your privacy, ProtonMail blocks tracking pixels and hides your IP address when you read emails, preventing advertisers from building profiles based on your email activity.
- Open source and audited: Transparency is key to ProtonMail's approach to security. Its applications are open source, allowing for community review and improvement. Furthermore, the code has been independently audited to ensure its security.
- Additional features: ProtonMail has implemented several other security measures, including hardware-level security, built-in PGP support, and innovative defenses against social engineering attacks.
Most secure social and messaging apps
Telegram
Signal isn't the only messaging app known for its strong security. Telegram, a cloud-based messaging platform that allows users to form groups and channels for sharing everything from text messages to files, offers comprehensive safety measures:
- Self-destruct secret chats: Telegram's secret chats feature end-to-end encryption, ensuring that messages can only be read by the sender and recipient. Users can set messages to self-destruct after a certain period, leaving no trace on Telegram's servers. Secret chats also prevent forwarding and notify users if a screenshot is taken.
- Public username option: Users can communicate without sharing their phone numbers by using a public username, enhancing privacy by keeping personal contact information hidden.
- Online status privacy: Telegram allows users to control who can see their online status or “last seen,” with customizable privacy settings to hide this information from specific users or groups.
- Active sessions management: The platform provides a feature to view and manage active sessions, enabling users to see all devices logged into their account and remotely log out from any that are unrecognized or no longer in use.
- Account self-destruct: Users can set their accounts to automatically delete if they are inactive for a specified period, ranging from 1 month to 1 year. This feature ensures that a user's data is not left vulnerable if they stop using Telegram.
- Encryption and data storage: Telegram uses its proprietary MTProto encryption protocol for all messages. It stores user data, such as IP addresses and device information, for up to 12 months, with the capability to provide this data to authorities if legally requested.
Earning itself a safety rating of 73% based on our criteria, WhatsApp has bolstered its security features to maintain user privacy and ensure secure communication. In addition to the end-to-end encryption across all chats and the deletion of messages from servers once delivered, WhatsApp has introduced several security measures:
- Account protect: This feature adds an extra layer of security when transferring your WhatsApp account to a new device. It verifies your identity on your old device to prevent unauthorized transfers, alerting you to potential unauthorized access attempts.
- Device verification: To combat mobile device malware, WhatsApp has implemented checks that authenticate your account without any required action from you. This feature is designed to protect your account even if your device is compromised, allowing uninterrupted use of WhatsApp.
- Automatic security codes: Enhancing the security for users who verify their chats manually, WhatsApp has introduced a feature based on “Key Transparency.” This allows for automatic verification of secure connections, making it easier for users to ensure they are communicating securely.
WhatsApp emphasizes user control when it comes to privacy and security. Users are encouraged to enable two-step verification for an added layer of protection and to only use the official version of WhatsApp to avoid privacy and security risks. The platform also provides tools for managing group safety, recognizing and avoiding scams, and options for users to report problematic behavior or block unwanted contacts.
Given Instagram's status as a prime target for hackers, the platform has deployed comprehensive security measures to safeguard user accounts and data:
- End-to-end encrypted chats: This feature is only available in some areas currently but helps protect your messages from being read by anyone, including Meta/Instagram.
- Suspicious login alerts: Instagram enhances account security by alerting users to suspicious logins. If someone logs into your account from an unknown device or location, Instagram sends a notification to confirm if it’s you. This feature allows users to act quickly by resetting their password if the login was unauthorized, helping to prevent unauthorized access.
- Emails from Instagram: This security measure ensures users can verify the authenticity of emails from Instagram. All official communication from Instagram about your account can be found under “Emails from Instagram” in the app settings. This feature helps users distinguish between genuine emails from Instagram and potential phishing attempts.
- Account recovery: Instagram has streamlined the account recovery process for hacked accounts. If your account is compromised, Instagram verifies your identity by sending a code to your registered email or phone number, enabling you to regain access and secure your account.
- Security checkup: This feature guides users through essential steps to secure their accounts, including checking login activity, updating personal profile information, and reviewing account recovery contact details. It's designed to ensure that all aspects of your account are protected.
- Instagram will never send you a DM: To combat phishing, Instagram emphasizes that it will never contact users via Direct Message (DM) for account issues. This policy helps users identify and report scam attempts. Instagram advises users to report suspicious content and accounts directly from the app.
- Login requests: When two-factor authentication is enabled, Instagram sends a login alert for attempts from unrecognized devices or browsers. Users can approve or deny these requests directly, offering an additional layer of security.
Snapchat
Snapchat's approach to security and privacy incorporates a variety of features aimed at creating a secure environment for its users. In addition to end-to-end encryption for photo and video “snaps”, Snapchat has designed its platform with several additional safeguards:
- Ghost mode and location settings: Snapchat allows users to control their visibility on Snap Map through Ghost Mode, ensuring location privacy by hiding their position from friends.
- Screenshot alerts: The app notifies users if someone takes a screenshot of their content, providing transparency and control over personal data shared.
- Privacy and safety by design: Snapchat emphasizes user safety from the start, with a focus on real-life connections and additional protections for younger users. It also prevents unvetted content from going viral.
- Content controls and reporting: Snapchat provides tools for managing interactions, including blocking or removing contacts and reporting issues or inappropriate content, thereby empowering users to curate their social experience safely.
- AI and chatbot interactions: The platform has incorporated AI features such as My AI, offering interactive chat functionalities while advising users on maintaining privacy and not sharing sensitive information. For added safety, Snapchat allows users to clear AI data through privacy controls.
- Family Center: This feature fosters open communication between parents and teens by allowing parents to see who their teens are messaging and their friend lists, without disclosing the content of the conversations. It also facilitates reporting concerns to Snapchat's safety teams.
Best shopping apps for user security
Amazon
Amazon, a leader in e-commerce, prioritizes customer transaction security by implementing a variety of measures, which are critical given the immense volume of personal and financial data processed by Amazon daily.
Amazon adopts several other strategies to enhance security:
- Protection of location and card data: Amazon safeguards your location and credit card information, ensuring that third-party sellers only receive necessary data for order fulfillment and that your payment information is kept confidential.
- Ratings and feedback system: A robust system allows customers to review seller ratings and feedback, contributing to a transparent shopping environment. This system also enables users to report suspicious or unreliable sellers, with Amazon taking appropriate actions based on these reports.
- Customer support and order tracking: Amazon provides extensive customer support and order tracking features, allowing users to resolve issues related to non-receipt of orders efficiently.
While your activity on Amazon’s app might be kept secure from attackers, it’s important to keep in mind that Amazon itself is known to mine user data and share it across its own services.
ASOS
The prominent fashion retailer is committed to ensuring the security of its user transactions and personal data, aligning with its strong stance on user privacy. Here are some of the key security measures ASOS employs:
- Limited data retention and secure data management: ASOS practices limited data retention, where messages delivered are deleted from servers to minimize the risk of data breaches, with undelivered messages stored for no more than 30 days. This approach is part of their broader strategy to manage and protect user data securely, including names, email addresses, and technical data like IP addresses.
- Data protection and transfer: In its commitment to user privacy, ASOS ensures that personal data collected for account creation, relationship management, and website analytics is handled with the utmost security. The company shares user data only with trusted entities within its group and professional service providers, such as marketing agencies and website hosts. Moreover, ASOS takes stringent steps to protect data when transferred outside of Europe, showcasing their dedication to global data security standards.
- User rights and data control: ASOS empowers its users with control over their personal information. Users have the right to access, modify, and delete their data, and can request account closure to stop receiving email alerts or other communications from ASOS. This level of control is part of ASOS’s comprehensive approach to security, ensuring users can manage their privacy and data security preferences effectively.
- Adherence to international privacy laws: ASOS’s security measures are in strict compliance with the General Data Protection Regulation (GDPR) and other relevant privacy laws, reflecting their commitment to safeguarding user data against unauthorized access and ensuring transparency in their data processing activities.
Most secure streaming platform app
Netflix
Netflix's security approach is multifaceted, encompassing several measures to ensure user data and account safety:
- Digital Rights Management (DRM): Netflix uses DRM to secure its content against piracy, ensuring that the copyrights of its shows and movies are protected. This not only prevents unauthorized distribution but also safeguards the content's integrity for legitimate viewers.
- Crackdown on password sharing: Although controversial, Netflix has introduced measures to ensure that accounts are used by authorized individuals only. This includes sending messages to users suspected of sharing passwords outside their household and asking for verification. Such steps aim to reduce unauthorized access and ensure that accounts are securely shared within the bounds of Netflix's terms of service.
- Regular security assessments and compliance: Netflix undergoes regular security assessments and audits to ensure compliance with industry standards and regulations. This includes adherence to the Payment Card Industry Data Security Standard (PCI DSS) for payment processing and privacy regulations such as the General Data Protection Regulation (GDPR) in Europe.
The Uber brand leads in app safety
Uber and Uber Eats
Reflecting their commitment to security with their high safety ratings of 73% and 79%, respectively, Uber and Uber Eats have implemented several advanced safety features to protect both personal data and financial transactions for their users.
Both platforms prioritize privacy by concealing phone numbers and address information during and after service delivery. For Uber Eats, this means that even though customers can be contacted by their delivery driver, the driver does not see the customer's phone number; calls are routed through Uber's system to maintain privacy.
Here are a few additional steps that both brands have taken to ensure user safety:
- Thorough background checks: Both drivers and delivery partners undergo comprehensive screenings for criminal history to enhance trust and safety.
- Using driver data to predict and mitigate risks: Uber analyzes past trip information and reported incidents to prevent potential conflicts on future trips.
- Privacy protection measures: After each trip, Uber removes address information from the driver's app, keeps users' last names and phone numbers private, and ensures the anonymity of customer ratings.
- Safety toolkit: This feature provides emergency assistance directly from the app, allowing users to call local emergency services with their location details. It also includes the Trusted Contacts feature for sharing trip details for added safety and ensures vehicle inspection standards are met.
- RideCheck technology: Utilizing sensors and GPS data, this system detects if a trip goes off-course or if a crash has occurred, offering support and resources to affected users.
- Commercial auto insurance: Uber maintains at least 1 million USD in liability insurance on behalf of drivers and delivery people once a ride or delivery is accepted, to protect riders and drivers in case of a covered accident.
- ADT partnership for live help: In collaboration with ADT, users can receive support via phone or text from a live safety agent during trips, including ongoing trip monitoring and emergency contact to 911 with essential trip details.
The top 5 apps for user privacy

Many apps and platforms make money by selling user data to advertisers and other third parties, often without clear consent. In fact, according to the Pew Research Center, 80% of Americans feel they have little to no control over their data collected by companies. This shows a significant concern over privacy breaches and the misuse of personal information. Privacy on apps empowers users to decide what information they share, with whom, and under what circumstances.
DuckDuckGo, Signal, and ProtonMail stand out for their strong privacy measures, which is why they also rank high for security on our list.
1. DuckDuckGo
DuckDuckGo is a pioneer in privacy-focused web searching, establishing a benchmark with its strict no-tracking policy. This policy is central to its operation; DuckDuckGo does not collect or share personal information on its users. Unlike many other search engines that create user profiles based on search history and browsing habits, DuckDuckGo ensures that every search is private, not recorded, and not used to profile users.
The app enhances user privacy by anonymizing searches. This means that when you use DuckDuckGo, your searches are decoupled from your personal information, such as your IP address. This anonymization ensures that your searches cannot be traced back to you, offering a layer of privacy that's rare in the search engine landscape.
Furthermore, DuckDuckGo employs encryption to protect users' search queries. By default, DuckDuckGo redirects users to the encrypted versions of websites, making it more difficult for third parties to intercept and understand users' activities online.
DuckDuckGo's commitment to privacy extends to its handling of ads and tracker blocking. While the service does show ads as a revenue model, these ads are based on the current search query rather than user history or profile. Moreover, DuckDuckGo blocks third-party trackers found on other websites, reducing the overall digital footprint left by a user across the web.
Lastly, DuckDuckGo offers a privacy score rating for websites visited through its search results. This feature educates users about the privacy practices of sites before they visit them, promoting an informed browsing experience. By grading websites from A to F based on their use of encryption and the presence of hidden trackers, DuckDuckGo empowers users to make privacy-conscious decisions about which websites to trust and engage with.
2. Signal
Signal is renowned for its stringent privacy measures, primarily through its implementation of end-to-end encryption for all forms of communication within the app, including messages, calls, and video chats. This encryption ensures that only the sender and recipient can access the content of communications, with no possibility for Signal or any third parties to intercept or decrypt these messages. This core feature is built on the Signal Protocol, which is widely regarded as the gold standard for secure communication.
Beyond encryption, Signal's privacy focus is evident in its minimal data retention policy. Unlike many other messaging platforms, Signal collects as little data as possible about its users. It does not store logs of who is messaging whom, or any metadata related to communications. The only information Signal retains is the date and time a user registered with the app and the last date of a user's app activity, which are used for minimal operational purposes only.
Signal also offers additional privacy features designed to give users more control over their communication and personal data. This includes disappearing messages, which allow users to set timers for how long messages remain visible after they've been seen, further reducing the amount of data stored on devices. Signal's Sealed Sender feature anonymizes the sender's information, making it impossible for even Signal to know who is messaging whom, enhancing privacy for both parties involved.
The app's commitment to transparency and security is also demonstrated through its open-source nature. Signal's code is publicly available for scrutiny, allowing experts to review and contribute to its security, ensuring that its privacy features remain robust against emerging threats.
Despite a recent incident with Signal's verification partner Twilio, where phone numbers of approximately 1,900 users were exposed, Signal's response emphasized its underlying privacy-first architecture. The breach never compromised message content or personal information, as Signal does not store such data. This incident highlighted the importance of external dependencies in the digital security ecosystem but did not detract from Signal's overall privacy and security model.
3. Tor Browser
Exclusively available on Google Play, the Tor Browser app is renowned for providing users with anonymity while browsing the internet through its encrypted network. Its core technology, onion routing, plays a pivotal role in achieving this level of privacy.
Onion routing is a sophisticated method of internet communication that encrypts user data in multiple layers and sends it through a series of relays around the world. Each relay peels away a single layer of encryption, only knowing the source of the incoming data and the next destination, but not the final recipient or the full path the data has taken. This makes it extraordinarily difficult for anyone to trace the internet activity back to the user, ensuring anonymity.
Tor Browser takes user consent seriously, with a clear privacy policy that outlines how data is managed and an explicit requirement for user consent before any data collection occurs. This transparent approach to data handling further cements its commitment to user privacy.
A critical feature of Tor Browser is its stringent no-tracking policy. Unlike conventional browsers that collect and store information about users’ browsing habits, Tor Browser does not log any search history or cookies, nor does it store any details about a user's browsing session. This policy ensures that users leave no digital footprint that could be used to identify them or their activities online.
Furthermore, Tor Browser's architecture inherently blocks many forms of surveillance and tracking by websites. It effectively counters fingerprinting techniques that attempt to identify users based on their device and browser settings, making it a robust tool for maintaining complete online privacy.
4. ProtonMail
ProtonMail stands sets the benchmark for email privacy, distinguishing itself with a suite of features designed to secure user communications. At the center of ProtonMail's privacy commitment is its use of end-to-end encryption for all emails. This encryption ensures that only the sender and recipient can read the contents of an email, effectively locking out any third-party access, including ProtonMail's servers. This level of encryption is automatic and transparent, requiring no technical knowledge from the user to activate or maintain.
Beyond encryption, ProtonMail is headquartered in Switzerland, a country known for its strong privacy laws. Operating under such jurisdiction means that ProtonMail benefits from legal protections that prevent unauthorized access to user data, reinforcing its privacy capabilities. Swiss privacy laws are among the strictest in the world, offering an additional layer of security to ProtonMail users.
ProtonMail's commitment to privacy extends to its minimal data retention policy. The service does not log personally identifiable information like IP addresses, ensuring that users' activities cannot be traced back to them. This policy is part of ProtonMail's broader approach to minimize data collection and maximize user control over their personal information.
Another notable feature of ProtonMail is the ability to send self-destructing emails. These emails automatically delete after a set period, leaving no trace on either the sender's or recipient's devices. This feature is particularly useful for sending sensitive information that should not be stored long-term.
ProtonMail also allows users to create accounts without providing personal information, offering an anonymous email service. This anonymity is crucial for users who prioritize privacy and wish to keep their identity separate from their email activities.
5. Session
Session is a messaging app focused on privacy, differentiating itself by not requiring a phone number or email address for signup. This unique approach enhances user privacy significantly, enabling complete anonymity. The foundation of Session's privacy strategy is its decentralized infrastructure, which employs blockchain technology to spread its operations across a multitude of servers worldwide. This decentralization eliminates a single point of control or failure, making it exceedingly challenging for any entity to access or censor user data, and offers protection against the vulnerabilities inherent in centralized data storage systems, such as the risk of mass data breaches.
A key aspect of Session's commitment to privacy is its minimal metadata logging. Many messaging apps collect metadata, which includes information on who users communicate with, when, and how often. In contrast, Session aims to collect as little metadata as possible. It utilizes an onion routing protocol, similar to Tor's technology, to send messages through several layers of encryption and relays. This process significantly obscures metadata, rendering the tracing of communication back to users nearly impossible.
Transparency is another cornerstone of Session's approach to privacy, underscored by its open-source code. This openness allows anyone to inspect and evaluate its security and privacy features, fostering trust among users and the broader tech community by facilitating independent verification of the app's privacy and security claims.
Moreover, Session supports private groups and sessions, allowing users to engage in secure communications with multiple individuals without sacrificing privacy. These conversations are also end-to-end encrypted, ensuring the confidentiality of group interactions. Furthermore, Session employs randomly generated session IDs to identify users, avoiding the need for personal identifiers such as phone numbers or email addresses. This feature is central to its privacy-first ethos, enabling users to interact anonymously and without disclosing any personally identifiable information to the app or to other users.
The best app for security and privacy: ExpressVPN
While we don’t mean to brag—considering our focus has been on showcasing the apps leading the charge in user privacy and security—it would be remiss not to highlight ExpressVPN’s pivotal role in this landscape. ExpressVPN is available for iOS, Android, Windows, MacOS, and Linux devices, with apps downloadable from the Apple App Store, Google Play Store, and directly from the ExpressVPN website.
| Security features | Privacy features |
| Robust encryption: ExpressVPN utilizes Advanced Encryption Standard (AES) with 256-bit keys. This level of encryption is the same standard adopted by security experts worldwide to protect classified information, keeping your data transmissions safe from attackers. | No-logs policy: ExpressVPN adheres to a strict no-logs policy, ensuring that your online activities, from browsing history to network traffic, are never recorded, tracked, or shared. This core principle guarantees that even ExpressVPN itself cannot see or store data about your online presence. |
| VPN protocols: Our app supports a variety of secure VPN protocols, including Lightway, OpenVPN, and IKEv2. These protocols are the backbone of our service, ensuring fast, secure, and reliable connections for all users. | Payment anonymity: Recognizing the importance of financial privacy, ExpressVPN offers anonymous payment options, including cryptocurrencies like Bitcoin. This feature allows users to subscribe to our services while maintaining their payment confidentiality. |
| Kill switch: ExpressVPN’s Internet Kill Switch is a safeguard that stops all internet traffic if the VPN connection drops unexpectedly, protecting your data from leaking during accidental disconnections. | IP address masking: With ExpressVPN, your real IP address is hidden from the websites you visit. Instead, websites see the IP address of our VPN server, enhancing your anonymity online and preventing tracking of your internet activity. |
| Independent audits: Transparency is key to trust, which is why ExpressVPN undergoes regular independent security audits. These audits verify our adherence to the highest standards of privacy and security, providing users with peace of mind. | TrustedServer technology: ExpressVPN’s TrustedServer technology ensures that all data on our servers is wiped with every reboot, as we run on RAM-only servers. This means no data is ever written to a hard drive, making it impossible to store any user information. |
| Tracker blocker: Our Threat Manager feature stops your device from communicating with known malicious sites and trackers. | DNS leak protection: ExpressVPN provides protection against DNS leaks, ensuring that all DNS requests are securely routed through our encrypted VPN tunnels. |
Gaming apps have the most problematic security features

Free gaming apps like Race Master 3D, Subway Surfers, Candy Crush Saga, and Stumble Guys draw in players with their addictive gameplay and colorful visuals. However, beneath the surface of these lies a concerning issue: a notable deficiency in essential security features. These popular titles, among others, consistently miss implementing critical security measures such as 2FA, strong encryption, and strong password protections, potentially putting users at risk.
This seemingly common oversight in the gaming app sector not only opens the door to potential data breaches and unauthorized access but also raises questions about the industry's commitment to protecting user privacy. While the reasons behind these lapses may vary—from a focus on seamless user experience to budget constraints—the implications for gamers are universally significant.
Security alerts for common app types
Beyond gaming, there are a few widely used app types that come with similar security concerns:
Free VPN services
Free VPNs often promise privacy and security but may fail in delivering robust protection. They might log user activity or offer inadequate encryption, leaving user data vulnerable to exposure. Users should be cautious of free VPNs that lack transparency about their data handling practices.
Older messaging apps
Older messaging apps like AIM (AOL Instant Messenger) and Yahoo Messenger lack modern security features such as end-to-end encryption and are particularly vulnerable to privacy breaches and data interception. These platforms often fail to secure messages effectively, leaving personal conversations exposed to potential eavesdropping.
Smart home (IoT) apps
Apps controlling IoT devices need to be consistently updated and designed with strong security features to prevent unauthorized access. Without these measures, these apps can become gateways for hackers to access personal networks.
To safeguard against security vulnerabilities in the apps you use, ensure you:
- Only use official app stores: Stick to downloading games from reputable sources like Google Play or the Apple App Store. These platforms enforce strict security guidelines for apps, reducing the risk of encountering malware.
- Scrutinize permission requests: Be wary of games asking for permissions that don't make sense for their functionality. A puzzle game asking for access to your contacts or location data is a red flag. Only grant permissions that are essential for the app to function.
- Research app security history: Before downloading a new game, take a moment to look up its security track record. Apps with a history of vulnerabilities or breaches warrant extra caution or even avoidance.
- Check developer reputation: Investigate the developer behind the game. Developers with a history of security issues in their apps might not be the safest bet for your next download. Online forums, reviews, and news articles can provide valuable insights into a developer's reliability.
Privacy concerns in popular apps
While many apps claim to prioritize user privacy, practices such as excessive data collection, ambiguous privacy policies, and unwarranted sharing of user information with third parties highlight a different reality. We uncover the apps that have raised flags for their questionable handling of user privacy, shining a light on how they may fall short in safeguarding personal information.
YouTube
It’s one of the most popular video-sharing platforms globally, however, YouTube has been under scrutiny for its privacy and security measures. A significant concern is the lack of transparency regarding the collection and use of voice and audio information. Users are left in the dark about how their data is utilized and shared, especially with third parties. This ambiguity is particularly alarming given YouTube's affiliation with Google, a company known for its extensive data-sharing practices.
In addition to these privacy issues, YouTube has encountered security problems. Notably, in 2023, the platform faced accusations of collecting data from users under 13 years old—a demographic supposedly protected by the creation of YouTube Kids. Despite the existence of this child-friendly alternative, investigations have revealed that minors often access the main site, potentially exposing their personal information or that of their guardians to cybersecurity risks. This situation raises questions about YouTube's commitment to protecting its younger audience and the effectiveness of its measures to segregate content and users by age.
TikTok
Despite its immense popularity as a video-sharing platform, TikTok faces significant scrutiny over its privacy and security practices. One of the critical shortcomings is the absence of end-to-end encryption—a standard security measure that ensures only the communicating users can access the messages or content shared between them. TikTok states that, while encryption is used, the company is able to decrypt user data as needed.
Furthermore, TikTok's approach to data sharing and privacy policies raises concerns. The platform lacks a transparent policy on how user data is shared with third-party entities for marketing purposes. This opacity leaves users in the dark about who has access to their information and for what reasons. Additionally, there's a notable lack of clarity regarding the management of user content. Questions about how content is stored, secured, and possibly utilized for training algorithms remain unanswered, contributing to the unease among its user base.
Compounding these issues, TikTok's privacy policy does little to educate its users about the available privacy settings and account types. This information gap can leave users, particularly the younger demographic that heavily populates the platform, vulnerable to privacy invasions due to a lack of control over content visibility.
In 2023, TikTok faced a hefty fine of 16.1 million USD for inadequate disclosure regarding third-party data sharing. This incident highlighted the platform's failure to communicate transparently about how user data and personal information are shared. Such practices have understandably heightened concerns, especially among the platform's predominant user group aged between 10 and 19, regarding their privacy and data security on TikTok.
Roblox
Despite its popularity among younger gamers, Roblox carries concerns related to data usage and privacy.
A significant issue is the app's handling of player data. Roblox users are left in the dark about the duration for which their data is retained, as the platform fails to specify storage timelines or usage details. Such ambiguity around data retention policies can lead to unease among users, who remain uncertain about the longevity and scope of their data's use on the platform.
Further adding to these privacy issues, Roblox's policy on the use of players' phone numbers is particularly troubling. The app mentions utilizing users' phone numbers but falls short of offering an opt-in choice for players. This lack of consent mechanism fails to empower users in deciding whether their personal information should be utilized by the platform.
AccuWeather
A leading name in weather forecasting services, AccuWeather isn’t immune to privacy and security controversies. Despite its utility in providing accurate weather predictions, the app has faced criticism over its handling of user data. Concerns primarily revolve around its data collection practices, specifically the transparency and consent related to sharing user information with third parties.
One of the main issues is AccuWeather's approach to user location data. The service has been accused of collecting and sharing precise location data with third-party advertisers without the explicit consent of its users. This practice raises significant privacy concerns, as location data can be sensitive and personally identifiable information that users may not wish to share broadly, especially without their knowledge or explicit approval.
Moreover, questions have been raised about the extent to which AccuWeather informs its users about the privacy settings and controls available to them. Users may find it challenging to navigate or understand the options they have to limit the sharing of their data, leading to a potential lack of control over their personal information.
Google Earth and Google Maps
Google Earth and Google Maps collect a lot of data, including where you go, what you search for, and how you use the apps. This data helps improve your experience but also raises privacy issues. Google's policy on sharing this data with third parties and for ads is not very clear, leaving users wanting more control and better explanations.
Similar to AccuWeather, location tracking is a key feature of these services. However, while it’s beneficial for accurate navigation, it also enables Google to amass detailed records of users' movements. If a user doesn’t manually disable this feature, it poses significant privacy risks and concerns over the potential for misuse of sensitive location information.
Moreover, Google Maps’ APIs are used by many other apps and websites, which could mean your data may be shared more widely than you think.
To keep your data private, here are a few practical tips to help safeguard your information when downloading and using apps:
- Review app permissions: Before installing an app, check what permissions it requests. Be wary of apps asking for access that isn't necessary for their functionality. Disable any permissions that you feel encroach on your privacy.
- Read privacy policies: While often lengthy, privacy policies can provide important insights into how an app uses, stores, and shares your data. Look for apps that commit to not selling your data to third parties.
- Limit location sharing: Only allow location access to apps when it's necessary for the app's functionality. For apps that don't need your location to work, keep this permission off. Also periodically check the permissions of apps on your device. Remove permissions that are not essential for the app to function.
- Use a premium VPN: A high-quality VPN like ExpressVPN can help protect your data on public Wi-Fi networks and conceal your activity from your internet service provider by encrypting your internet connection.
- Keep apps updated: Regularly update your apps to benefit from the latest security patches and privacy enhancements. If you're not using an app, it's best to delete it. This minimizes the amount of data potentially being collected about you.
Methodology
The methodology for ExpressVPN’s “App-roval” report evaluates mobile apps' security and privacy protection. We selected popular apps from various categories, including social media, entertainment, sports, gaming, food, shopping, and travel. Our assessment criteria included:
- App/Google store ratings.
- History of data breaches.
- Availability and cost of in-app purchases.
- Security features like encryption, 2FA, and password protection options*.
- The existence of a privacy policy and the type of user information collected.
Each app was scored out of 10 for each metric. This score was then converted to a percentage to indicate the app’s safety rating. Higher scores indicate better security and privacy protection for users.
*Password protection was gauged by whether the app offers settings for enhanced account security, such as requiring a secure password, enabling Face ID or a passcode for access, or the option to set a password for certain app sections (e.g., messaging).
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN