Predator spyware explained: How it works and how to reduce risk
Predator is commercial mobile spyware used in highly targeted surveillance operations.
Unlike ordinary spyware, which is often spread through phishing, malicious downloads, or deceptive apps, Predator is typically associated with attacks on a small number of specific individuals. Those targets are often chosen because of their role, work, or access to sensitive information.
This guide explains how Predator differs from other spyware, how infections typically happen, who is often targeted, and what practical steps can reduce risk.
How does Predator spyware differ from other spyware?
Predator differs from other spyware in how it’s developed, deployed, and used. It’s typically associated with highly targeted operations that involve significant resources, rather than broad, opportunistic campaigns. As a result, it relies on more advanced surveillance techniques and infrastructure.
It’s also part of a broader commercial surveillance ecosystem. Reporting from Amnesty International’s Predator Files suggests it’s developed and delivered through a business model built around targeted surveillance tools, rather than operating as a standalone piece of malware.
This helps distinguish Predator from more commonly encountered spyware, such as stalkerware. Stalkerware is typically used for interpersonal monitoring, such as tracking a partner or family member. Predator, by contrast, is more often discussed in the context of surveillance targeting journalists, officials, and other high-profile individuals.
| Type | Commodity spyware | Mercenary spyware (Predator-style) | Stalkerware |
| Aim | Steal data at scale | Targeted surveillance | Interpersonal monitoring |
| Targeting | Broad and opportunistic | Small number of high-value targets | Often someone known to the target |
| Delivery | Malicious apps, mass phishing, malicious downloads | One-click links, exploit chains, network injection, and, in some reports, zero-click capabilities | Physical access, installed monitoring apps |
| Detection | Antivirus and mobile security tooling | Forensics and known indicators | Safety-first checks, account review, and support resources |
How do Predator infections typically happen?
As noted above, Predator isn’t delivered through mass spam or random “drive-by” malware campaigns. Reported public cases show targeted delivery, in which the operator attempts to reach a specific person and trigger an exploit chain on that person’s device.
An exploit chain is a sequence of technical steps used to turn an initial contact into a full device compromise. For example, a malicious link or redirect might trigger one vulnerability, then use one or more additional flaws to gain deeper access and install the spyware.
Several main routes keep appearing in Predator-style campaigns, even as the technical details change over time. Below are the main paths researchers have repeatedly documented.
One-click links and targeted lures
One-click delivery is the simplest pattern. A target receives a link or is directed to malicious content and interacts with it, and the infection attempt begins. This has included links sent through messaging apps, as well as web-based delivery. Even when the content looks ordinary, a single tap or click can bring the device into contact with an exploit chain or infection infrastructure.
Operators tend to keep these links tightly controlled, because the fewer people who see them, the harder they are to capture and analyze. In some cases, the links check details about the device or browser fingerprint before delivering the exploit, which helps ensure that only the intended target is affected. That is one reason you’ll see references to “one-time links” in threat analyses of Predator-linked activity.
On-path interception and redirects during HTTP browsing
A second pattern is traffic interception, often described as a man-in-the-middle attack (MITM). In this setup, the attacker sits between the target and the site they’re trying to reach and can intercept or alter data traveling between them.
Zero-day exploit chains
A zero-day attack exploits a previously unknown vulnerability, meaning the vendor hasn’t had a chance to patch it before it’s used.
In these cases, you may see identifiers like CVE-2023-41993, which are standardized labels used to track known vulnerabilities once they’re disclosed.
In September 2023, Google’s Threat Analysis Group reported Predator spyware activity in Egypt, including an iPhone exploit chain that targeted vulnerabilities in iOS versions through 16.6.1. The chain involved three vulnerabilities (CVE-2023-41991, CVE-2023-41992, and CVE-2023-41993) that Apple later patched in iOS 16.7 and iOS 17.0.1.
How does Predator operate after infection?
After Predator gets onto a device, it relies on backend infrastructure to function. In simple terms, these are remote systems that help install the spyware, maintain communication with the operator, and transmit collected data.
Researchers have described an “installation server” that delivers exploit code and the spyware payload, followed by additional systems that let operators send instructions and retrieve data.
In some cases, this setup makes it harder to identify who is behind the attack. In its report, Amnesty International describes a command-and-control (C2) anonymization layer meant to hide the operator behind the campaign. That helps explain why investigators can sometimes link servers or domains to Predator but still can’t say with confidence who was running the operation.
What can Predator spyware do on a compromised device?
Predator is described as capable of accessing sensitive data stored and transmitted from the target’s device.
The U.S. Treasury has listed examples of accessible information, including photos, geolocation data, personal messages, microphone recordings, contacts, and call logs. In a successful infection, operators may be able to retrieve and monitor this data directly from the device.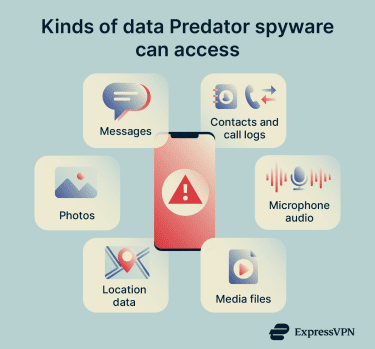
It’s worth noting that, if the device itself has been compromised, spyware may be able to access message content after it's been decrypted on the device, without breaking the encryption of the messaging service itself.
Who built Predator and who is associated with it?
Predator is commonly associated with the Intellexa network, a web of entities across multiple jurisdictions. Here are the entities that the U.S. Treasury describes as part of that network:
| Intellexa network entity | Where it's based | Place in the ecosystem |
| Intellexa S.A. | Greece | A software development company within the consortium. |
| Intellexa Limited | Ireland | A technology reseller holding assets on behalf of the consortium. |
| Thalestris Limited | Ireland | A financial holding company for the consortium. |
| Cytrox AD | North Macedonia | A Predator developer within the consortium. |
| Cytrox Holdings ZRT | Hungary | Previously developed Predator before production moved to Cytrox AD. |
| Aliada Group Inc. | British Virgin Islands | Consortium member that enabled tens of millions of dollars in transactions involving the network and held shares in Cytrox Holdings. |
Who is most at risk from Predator spyware?
These are the groups that appear repeatedly in official statements and technical investigations about Predator spyware. In some cases, researchers confirmed successful infections; in others, they documented attempted targeting through Predator-linked links or infrastructure.
- Government officials and public sector decision-makers: These roles are likely targeted because they often involve sensitive communications and institutional access.
- Journalists and media workers: Journalists can be targeted because their devices may contain source communications, unpublished reporting, and contact networks.
- Researchers, policy experts, and think tanks: “Policy experts” is a broad bucket, but it usually means researchers, advisers, and analysts who influence public decision-making or have access to sensitive discussions.
- Opposition politicians and politically exposed individuals: These targets can be attractive because spyware access can reveal strategy, communications networks, and real-world movement patterns.
- Activists, human rights defenders, and civil society leaders: “Civil society” generally means people and organizations working outside government, such as non-governmental organizations (NGOs), advocacy groups, and independent organizers.
- Lawyers and legal advocates in sensitive contexts: Legal work can be high-risk when it involves human rights cases, political defense, or high-profile accountability efforts.
What to do if you might be a target
Predator isn’t a risk for most people. But for those in higher-risk roles or situations listed above, it makes sense to focus on practical steps that reduce exposure and preserve options for expert help.
These are the baseline steps that matter most:
- Keep your phone and apps updated: Install operating system and app updates as soon as possible, because security patches close known vulnerabilities that attackers reuse at scale. Keep browsers updated too, since mobile exploit chains often start in the browser.
- Restart your device regularly: Some advanced spyware avoids building in persistence (the ability to stay installed after a reboot) because persistence can be technically difficult and may make the malware easier to detect. Restarting your device won’t guarantee protection, but it can interrupt certain infections and force attackers to reinfect the device.
- Treat unexpected links as unsafe: Assume a link is hostile until you verify it, especially if the message creates urgency, asks you to log in, or pushes you to open a document. If a message claims to be from an organization, go to the site or app directly instead of using the link, because phishing often relies on getting you to “follow the path” the attacker controls.

- Use strong, unique passwords: Use a different password for every important account. A password manager helps here because it can generate long, random passwords and store them securely, so you don’t end up recycling the same one.
- Install apps from official stores and review permissions: Stick to official app stores and be cautious with sideloading. When you install an app, check whether the permissions it requests match what it claims to do, because overbroad permissions can increase the damage if an app turns out to be untrustworthy.
- Use mobile security tools: Security apps can help detect known threats, flag suspicious behavior, and warn about risky apps or links. They don’t reliably stop advanced spyware on their own, but they can add visibility and reduce exposure to more common threats.
Extra steps if you’re in a higher-risk group
If you face a higher risk of targeted surveillance, here’s how to further reduce exposure:
- Shrink your attack surface: Consider device hardening options designed for targeted threats, such as Lockdown Mode on iPhone.
- Prefer safe browsing habits: Reducing exposure to insecure HTTP connections helps cut off one of the cleanest openings for on-path injection attacks.
Next, watch for credible triggers:
- Apple’s spyware threat notifications: Treat these as a strong reason to escalate to expert help, even though they’re not framed as absolute proof of infection.
- Highly specific, repeated lures: Suspicious messages tailored to your work, contacts, travel, or current events.
- Unusual redirects on mobile data: In documented Predator cases, on-path injection triggered redirects when targets browsed non-HTTPS sites.

Lastly, here’s what to do if you suspect targeting:
- Preserve evidence: Save suspicious messages, links, sender details, and timestamps.
- Get expert help early: Apple points users who receive threat notifications to specialist support resources, including Access Now’s Digital Security Helpline.
- Avoid factory resets until you have a plan: Wiping can remove forensic traces that would have helped confirm compromise and guide next steps.
- Be realistic about tools: Forensic toolkits exist for evidence collection and indicator checks, but they’re technical tools and don’t equal a consumer “virus scan.”
FAQ: Common questions about Predator spyware
What is Predator spyware?
Can antivirus software detect Predator spyware?
How does Predator spyware infect devices?
Can I detect Predator spyware on my device?
How can I protect my device from Predator spyware?
Can a factory reset remove Predator spyware?
Does a VPN protect against Predator?
Is keeping my device updated enough to protect against Predator?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN

















Comments
Why not just take all of this industry out of the equation completely for 30 days, six months, and require a standing pledge of allegiance in full. Before ANYONE can access their lock screens to access their own executioners? Sounds fair enough how bout a demerit suspension revocation system like china, I mean the old world USA?