On the internet, as most people use it, a domain name (e.g., expressvpn.com) is registered through a registrar. You usually pay a fee for this.
The part after the dot on the right of the domain, like “.com” or “.ca”, is called the top-level domain. It is often the code of a country, but some generic top level domains like “.website” also exist. Recently companies have even been able to register their own top-level domains, like “.apple”.
[Interested in privacy and technology? Sign up for the ExpressVPN Blog Newsletter.]
These top level domains are assigned by the Internet Corporation for Assigned Names and Numbers (ICANN). If you want to create your own top-level domain, you will have to submit your proposal and will likely pay a lot of money for it.
The part before the dot, on the left of the domain, is the subdomain. When you purchase a domain name, such as yourname.com, you are free to create subdomains and point them at separate servers, (e.g., blog.yourname.com or chat.yourname.com).
Once you registered your own domain with a registrar (or even a top level domain with ICANN), you can point this domain to the IP address of your website using a nameserver.
For a free and open internet, this creates various problems.
If ICANN take a disliking to you, for any reason, they can simply take away your domain and give it to someone else.
An attacker can get access to your account with the registrar and point it at their own server. They can use this to phish passwords and other privileged information from your users. Your server is always easily identifiable through your domain, which makes it easy to censor or confiscate your service.
.onion services address all these problems through clever cryptography and a few tricks.
A hash of a public key
Onion sites, like tp7q4m5ln4yhk5os.onion, are not registered. Instead, they are a hash of a public key.
To be precise, a Version 2 onion domain is the first half of the base32 encoded SHA-1 hash of a public key, from a 1024-bit RSA key pair with the suffix “.onion”.
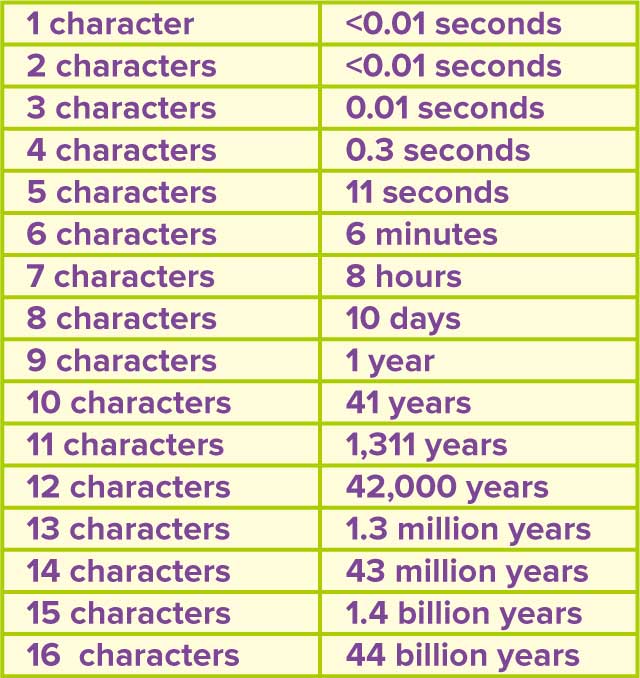
The result is that a .onion domain name will be 16 characters long and can only contain lowercase letters a to z and the digits 2 through 7.
Recently you might have come across longer onion addresses. These “Version 3” names are longer (56 characters) and make use of more robust hash functions, such as SHA3. Instead of a 1024-bit RSA key, they are making use of elliptic curves (curve25519). This makes Version 3 addresses more private and robust against impersonation.
When you type a .onion address into your Tor browser, unlike with a regular domain, you are not looking up an IP address on a DNS server. Instead, you are asking a Hidden Service directory, which anybody can volunteer to run.
If the Hidden Service directory you are requesting knows how to find the server you are looking for, you will be directed to the website, without the location of it being revealed (learn more about how Tor works here).
.onion recognition from internet registrars
Because this functionality only works in the Tor network, you will only be able to look up .onion websites through the Tor browser. If ICANN were ever to issue domains with the ending .onion, however, this could create a lot of confusion, as hidden services and sites in the regular net would resolve the same address in two different ways, leading to two different sites.
This is not very likely, however, as ICANN is likely to recognize the broad adoption and usage of the Tor network, and would certainly want to avoid confusion across the domain name system.
The Internet Engineering Task Force, IETF, which develops and maintains internet standards like TCP/IP has already formally recognized the .onion domain in what was hailed as a landmark decision in 2015. This decision came after heavy lobbying from the Tor Project and made it possible for Facebook to receive a digital TLS certificate.
TLS is not needed in the Tor network for encryption, as the connection is already end-to-end encrypted between a .onion server and the user. A certificate, however, makes it easier for the user to verify they are connecting to the right server and provides an additional barrier for an attacker.
Getting a vanity .onion address
When you generate a .onion address, it will look rather random, as is the case with any hash. However, statistically speaking, if you create enough such addresses, once in a while you will randomly stumble upon one which is actually readable.
For each position, there are 32 possible characters. If you want to find an address that starts with e, you expect to have to guess about 16 times. If you want an address starting with ex, you already have to guess (32*32)/2=512 times. For exp, over 16,000 guesses are needed.
A modern computer can, using a script, easily guess about 1-2 million such addresses per second. From here we can easily estimate how long it would take us to find the domain name we want. We could use the same process to try to crack somebody else’s .onion address, but the following charts show you that this would not be feasible.
To generate a good, memorizable and aesthetic .onion address, you will not limit yourself to simply looking at the first characters. You can use regular expressions to create patterns that are easy to read and remember.
To generate their .onion domain facebookcorewwwi.onion, Facebook took a new datacenter and used over 500,000 cores to generate domains over and over until they found one that they liked.
It took Facebook over one week to generate their .onion domain, and the computing power would have cost around US$100,000 in electricity.
Nik Cubrilovic, who set up the hidden service for Blockchain, says it only took them 200-300 USD and about 24h to come up with their domain (blockchainbdgpzk.onion) using an AWS G1 instance and a cluster of six ATi cards.
ExpressVPN only used a single computer with a freshly installed operating system. The computer was not connected to the internet to limit the risk of a third party getting hold of the keys. It took about two weeks to generate expressobutiolem.onion, as well as a couple of other less aesthetic domains.
.onion address security
While you wouldn’t be able to crack a .onion key with your laptop or even a thousand laptops, you might be able to if you find a million computers that each has about 10,000 times the computing power of your laptop today.
Even then it might take you a few years, but what sounds outrageously expensive today might soon come within reach of a well funded and motivated three-letter agency.
In the future, .onion addresses will have to be upgraded, or a new scheme will have to be found. At the very least, the RSA key will have to be extended (ExpressVPN already uses RSA keys with a length of 4096 bits for its VPN service) and the hashing algorithm could be upgraded to an SHA-2 algorithm.
Bitcoin addresses, for example, are created very similarly to .onion addresses, but Bitcoin uses the ECDSA elliptic curve to generate keys of 256 bits and applies the SHA-256 hashing function twice to derive the address.
Where next for Tor and .onion?
We don’t know what the future will hold for .onion address TLS certificates. As .onion addresses are hard to calculate, there is little risk of them being copied, but users can still be tricked into following a similar address and getting phished. To avoid this, the user needs to check the integrity of the entire domain, not just the first few matching characters.
TLS certificates potentially make this process easier, but it also requires the holder of the .onion key to reveal their real identity.That would undermine the very purpose of the hidden service.
One alternative would be to use mapping services like Namecoin or Blockstack to create a decentralized DNS replacement. However, it’s unclear how such a system could deal with name squatting and phishing. In the end, the future may even belong to simple combinations of long cryptographic hashes and ordinary address books.
Have your own theories about the future of .onion domains? Share your thoughts in the comments below!
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN













Comments
How can I Register on my iPhone 6, it’s keep telling me check your networks or contact us on the app downloaded on my phone. I have the license key on my laptop but I can’t register on my phone. Any help
Hi Olaoye, please contact Support and they will help you finish the setup.
And now we have Version 3 onion addresses which are much longer and therefore much more difficult to crack. So, the 44 billion year mark has skyrocketed through the roof.