How to know if your computer has a virus (Windows and Mac)

Computer viruses and other malware affect both Windows and macOS systems. Some types cause obvious disruptions: endless pop-ups, crashing apps, or a system that slows to a crawl. Others are designed for stealth, quietly stealing data or turning off protections in the background.
The signs of infection usually show up as repeating patterns: files that go missing, security settings that switch off on their own, ads that keep returning, or unexplained system slowdowns. None of these issues alone proves infection, but when several appear together and persist after restarts, malware becomes the most likely explanation.
This guide explains how to know if your computer has a virus and takes you through the steps to detect and remove malware safely and prevent further infections. It also explains the main types of malware and how these infections can spread.
Signs your computer might be infected with a virus
The list below covers the most common indicators of potential infections on Windows and macOS.
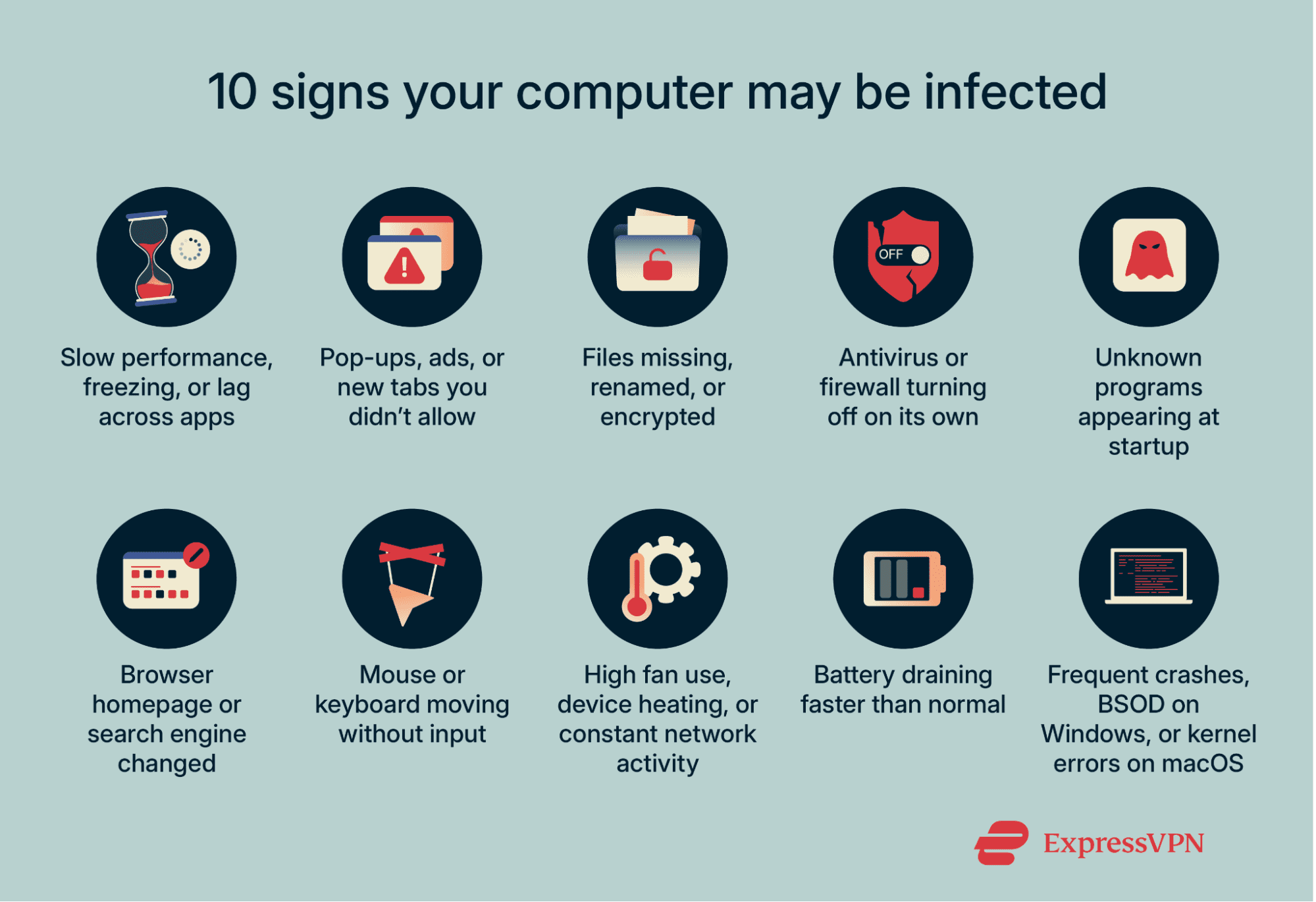
1. Slow performance or freezing
Applications open more slowly than usual, the cursor stutters, or the screen freezes during simple tasks like opening a folder or switching tabs. If this sluggish behavior persists across different programs and returns even after you restart your system, it can be a sign of malware consuming system resources in the background.
2. Random pop-ups and unwanted ads
New tabs or windows appear on their own, ads show up on websites that normally don’t display them, or notifications arrive from sites you never approved. When these pop-ups recur across unrelated sites or even after you reset your browser settings, adware or other unwanted software is a likely cause.
3. Files disappearing or becoming corrupted
Documents may vanish, refuse to open, or appear with altered names and extensions. In some cases, files are replaced with encrypted versions that display ransom notes, or shortcuts stop working altogether. Unexplained file corruption is one of the main warning signs of infection.
4. Built-in security features turning off unexpectedly
Antivirus real-time protection disables itself, the firewall switches off, or security definitions fail to update while the internet connection is stable. These features can sometimes fail for other reasons, but repeated deactivation without your input can be an indicator of malware interference.
5. New or unknown programs running
A program you don’t recall installing shows up in your installed apps. The system tray or menu bar displays new icons, and unfamiliar items launch automatically after sign-in. While some preinstalled utilities may update themselves, truly unexplained additions may indicate malware.
6. Changes to your browser homepage
Your search engine, homepage, or new tab page changes without permission. Searches redirect through unfamiliar search engines you didn’t choose, or shortcuts open to unexpected sites. These changes often come from browser hijackers or hidden extensions.
7. Devices acting on their own (mouse, keyboard)
The pointer may move without input, text may appear in fields while you’re not typing, or windows may open and close unexpectedly. While this may be a sign of malware, note that faulty peripherals, wireless interference, or driver issues can produce similar effects, so always test with another mouse or keyboard first.
If the activity continues across different input devices and applications, it may indicate remote access malware such as a Remote Access Trojan (RAT). These tools give attackers full control of the system, letting them type, move the cursor, copy files, or install other malicious programs.
8. Strange background activity
Fans may surge when the computer is idle, the device may stay warm during light tasks, or the network indicator may blink even when no apps are open. Normal processes like system updates or cloud backups can explain occasional spikes in CPU usage, but constant unexplained activity across multiple sessions often comes from malware running background tasks.
9. Battery draining faster than normal
The battery may drop quickly during simple tasks, consume more power in sleep mode, or leave the device warm when it should be cool. Updates, indexing, and certain high CPU-usage tasks can cause short-term drain, but when the problem continues without a clear cause, it may indicate malicious processes consuming resources in the background.
10. System crashes or frequent restarts
On Windows, this often appears as a blue screen (commonly called the Blue Screen of Death, or BSOD). On Mac, it might appear as a kernel panic error, which forces your device to restart unexpectedly. Hardware faults and driver conflicts can also cause crashes, but if they happen repeatedly without recent hardware changes or updates, it may point to malware tampering with system files.
How do computers get viruses?
There are many ways your computer can get viruses. Let’s look at some common entry points:
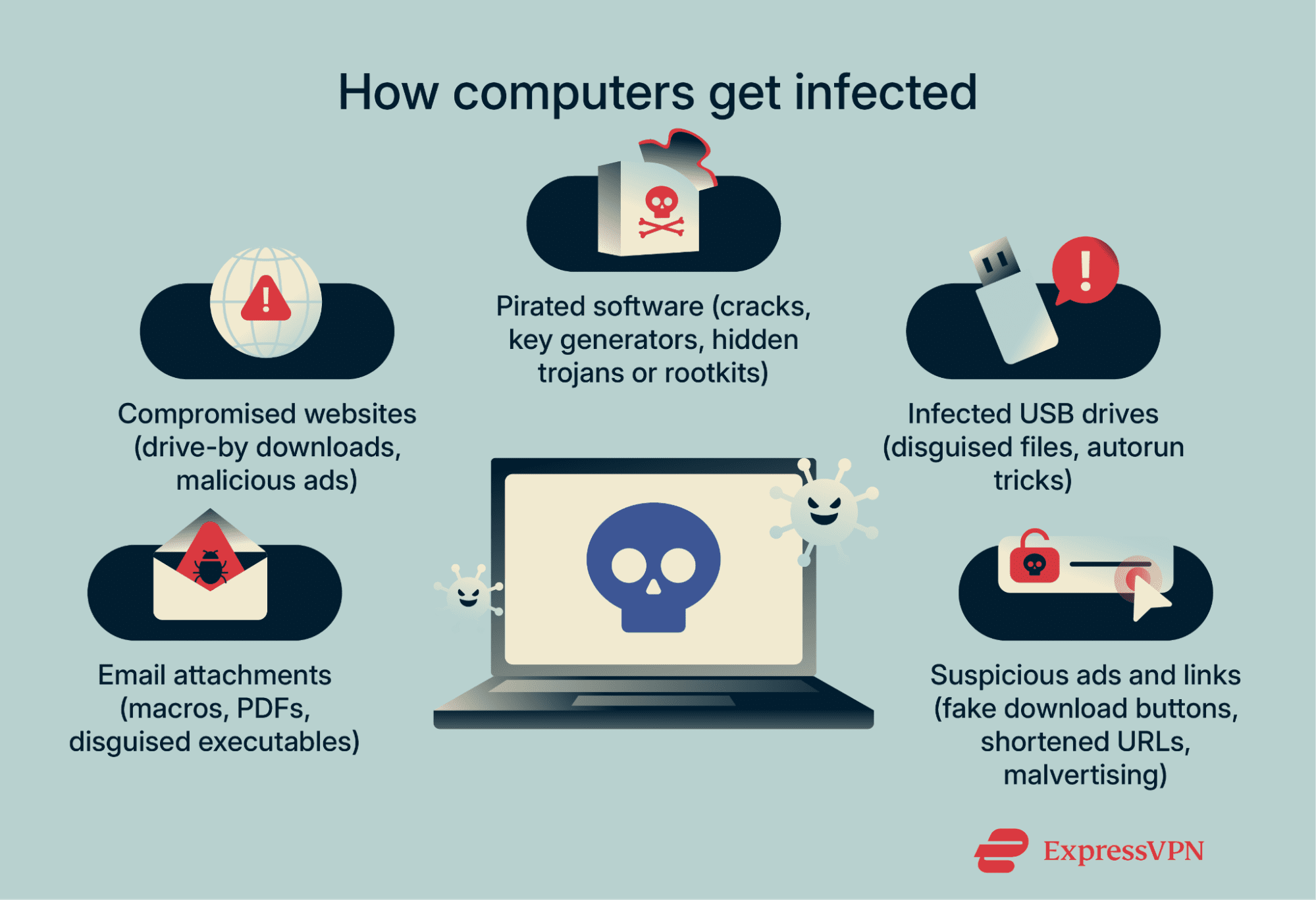
Unsafe email attachments
Attackers often send emails that look like invoices, shipping updates, resumes, or account alerts. These messages may include attachments that carry hidden code, such as:
- Macro-enabled Office documents: Word or Excel files that contain embedded scripts (called macros). If macros are enabled, the script runs and installs malware.
- PDFs with embedded scripts: A PDF that contains JavaScript, which can trigger unwanted downloads when opened.
- Compressed archives: Files like ZIP or RAR bundles that contain disguised executables (programs that run when opened) instead of harmless documents.
These emails often try to create a sense of urgency or fear, prompting you to open attachments or click links without thinking.
Visiting compromised websites
Even well-known or reputable websites can occasionally be compromised. One risk is a drive-by download, where code may execute automatically if the browser or plugins are outdated or misconfigured. Malicious ads placed on legitimate sites can also redirect visitors to unsafe downloads or phishing pages.
Downloading cracked software or games
Pirated applications and key generators (programs that claim to unlock paid software) can include hidden malware. While the software may appear to function normally, it can silently install trojans, spyware, or adware. In some cases, more advanced threats like rootkits are used to hide malicious activity, and some malware may connect to external servers to receive updates or additional files.
Using infected USB drives
USB drives can spread malware in several ways. Some are infected before you receive them, such as during manufacturing, distribution, or repackaging, and contain files that execute when opened, installing malware on the system.
Attackers may also use USB drop attacks, leaving preloaded drives in public places or sending them to targets by mail. These drives often contain files disguised as ordinary documents or shortcuts, which execute malicious code once opened.
Older versions of Windows included an autorun feature that automatically launched software when a drive was inserted. This feature is now disabled by default (Microsoft disabled it in Windows 7 and later), but some attacks still rely on social engineering, prompting users to click on pop-ups or modified shortcuts to trigger malware execution when a USB is connected.
Clicking suspicious ads or links
Deceptive buttons labeled “Download,” “Play,” or “Update” can install malware instead of the file they claim to deliver. Attackers may also use shortened links in emails or social media posts to disguise the real destination, making it easier to direct users to malicious websites.
Another tactic is malvertising, where harmful ads are injected through ad networks and may even end up on legitimate websites. These ads often rotate between domains to avoid being blocked. They may urge you to install extra software such as a codec (a program that helps play audio or video files), a system cleaner that promises to speed up your device, or a fake update for an application you already use.
Types of computer viruses
People often use the word “virus” to describe any kind of malicious software. In reality, malware is the broader category that includes viruses, trojans, worms, spyware, ransomware, adware, and more. The examples below show how different families of malware behave on consumer systems.
File-infecting virus
A file-infecting virus attaches itself to executable files. When the infected program launches, the virus activates and spreads by inserting code into other executables on the same device or shared drives. The impact ranges from subtle interference to visible corruption.
Certain variants attempt to block updates or interfere with antivirus components to remain active. Because they alter files directly, recovery without a clean backup is often difficult.
Browser hijacker
A browser hijacker changes your browsing settings without permission. It may reset your default search engine, homepage, or new tab page. Some versions add extensions, inject ads, or rewrite search results to send traffic through partner networks.
On macOS, system-wide settings can be applied through configuration profiles. These are files normally used by schools or companies to manage devices; they can set Wi-Fi networks, VPNs, or browser defaults. A malicious profile can hijack that same mechanism to lock the browser’s default search engine.
Instead of you being able to choose a browser like Google, DuckDuckGo, or Bing in your settings, the hijacker enforces its own search provider (like a shady redirect engine). If a malicious profile is installed, changing the setting back manually won’t work, since the profile forces the hijacker’s choice.
Network-spreading virus
Also known as a worm, this type of malware spreads automatically across local networks and connected devices. It scans for open services, weak passwords, or unpatched vulnerabilities, then copies itself without requiring user action. Once inside, it may deploy additional payloads (the harmful component of the attack), like spyware, cryptocurrency miners, or ransomware.
Home networks aren’t immune; devices such as outdated printers and unsecured smart devices can be exploited because they stay online and are rarely updated.
Trojan horse
A trojan disguises itself as a legitimate app or document and asks for permissions it doesn’t need. Once opened, it delivers hidden payloads. These can include spyware that monitors browsing, adware that injects ads, keyloggers that record every keystroke, or remote access tools that allow attackers full control of your system.
Trojans often spread through cracked software or fake update prompts. Many add themselves to system startup tasks or login items so they can still relaunch after a reboot.
Polymorphic virus
A polymorphic virus modifies its own code or encryption each time it spreads. This means every copy looks different at the byte level, making traditional signature-based detection (where antivirus tools look for a known digital fingerprint) less effective.
The behavior, however, stays the same: replicating, corrupting files, and trying to persist on the system. That’s why modern antivirus software combines signatures with heuristics (rules for spotting suspicious behavior) and real-time monitoring that analyzes how programs act under different conditions.
What can a virus do to your system?
Steal or corrupt data
Malware can silently gather sensitive information, including passwords, payment details, and saved login tokens that grant access to email or cloud accounts. Some spyware families request or exploit access to webcams or microphones, enabling ongoing surveillance in addition to data theft.
Corruption damages the integrity of work that hasn’t been backed up, leaving files unusable even if they aren’t stolen.
Slow down system operations
Malware often installs background processes that never stop running. For example, cryptocurrency miners may use your computer’s hardware to generate digital coins for attackers, consuming both processing power and electricity. Adware can also overload the browser with pop-ups or scripts that eat up memory and make normal browsing sluggish.
Disable security features
Many malware families attempt to weaken a system’s built-in defenses so they can persist longer. They may:
- Switch off real-time protection in antivirus tools, leaving the system unable to block threats as they run.
- Block security definition updates, preventing the antivirus from recognizing new malware types.
- Alter firewall rules, opening connections that allow remote access or stopping the firewall from blocking suspicious traffic.
- Delay or disable operating system patches, ensuring known vulnerabilities remain unpatched and exploitable.
Lock you out of your files or system
Ransomware is built to deny access until a ransom is paid. It may encrypt personal folders, block the entire system volume so the operating system won’t load, or replace the desktop with a full-screen ransom message.
To stop recovery, many strains disable or erase local restore points, the automatic backups created by Windows. Modern families also combine encryption with data theft, stealing files first and then threatening to publish them.
Spread beyond your device
In some cases, an infected machine becomes a launch point for wider attacks. Worm-like malware can move laterally to other computers on the same network, and botnet malware can use your connection to send spam, host phishing pages, or launch denial-of-service (DoS) attacks. This not only harms your system but also puts others at risk, and it may cause your IP address to be blacklisted.
How to detect and remove a virus
The goal of virus removal is to isolate the device, confirm the infection, and clean it without risking data loss. Work in a sequence: start with isolation, use built-in tools or antivirus software first, then escalate to a system restore if needed. Keep a record of every change you make so you can undo mistakes later.

Disconnect from the internet during troubleshooting
The first step is containment, so it’s important to turn off Wi-Fi and unplug Ethernet cables before you begin. This prevents the malware from contacting attacker servers, downloading additional components, or transmitting stolen data.
If you need to download cleanup tools, use a separate, uninfected computer and transfer files with a freshly formatted USB drive. Leave the infected device offline until the cleanup is complete.
Run a full system scan using built-in tools
Before adding new software, make full use of the protections included with your operating system. Quick scans are faster but may miss deeply embedded threats, while full scans take longer and are more reliable.
Windows 11
- Open Windows Security from the Start menu.
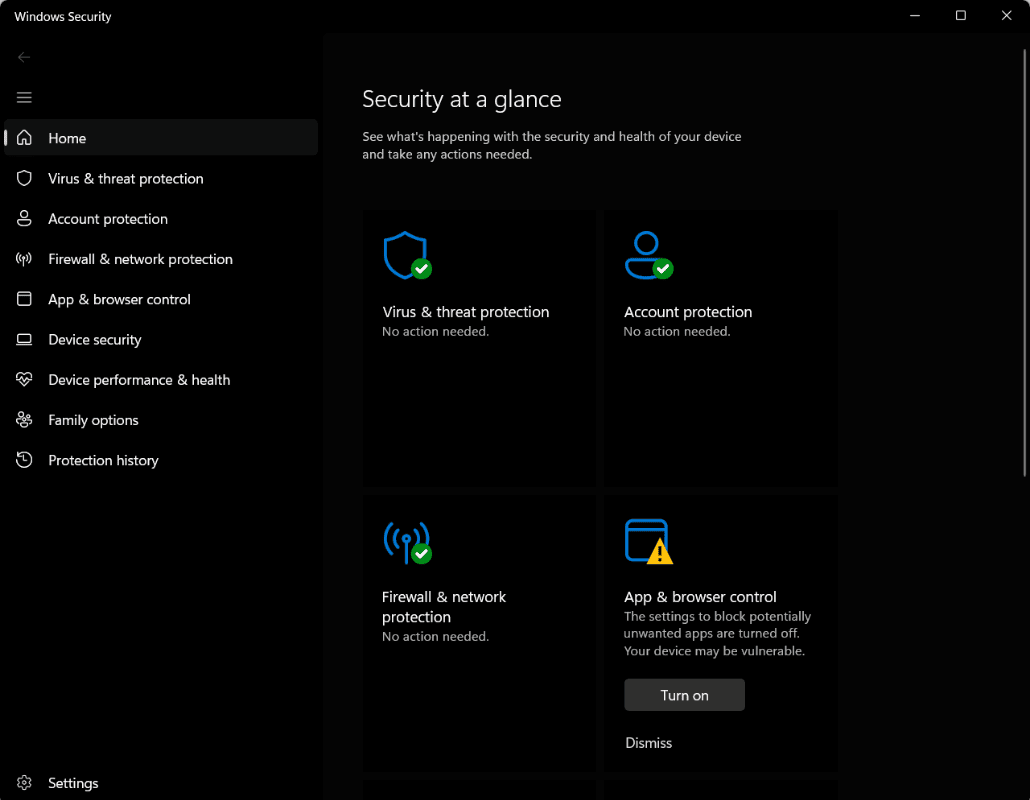
- Select Virus & threat protection > Scan options > Full scan. A full scan can take anywhere from a few hours to several days, depending on the amount and type of data stored on your drives.
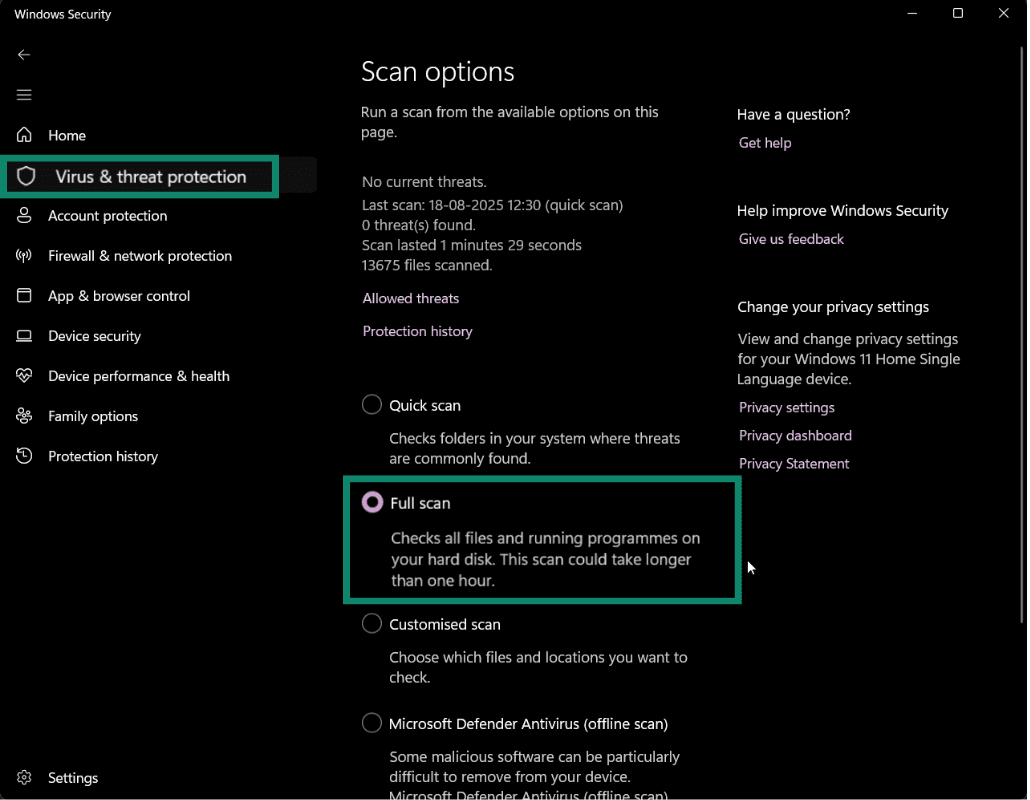
- If threats are detected, choose Quarantine instead of Delete. Quarantined files are isolated so they can’t run, but in case of any false positives, they can be restored if needed.
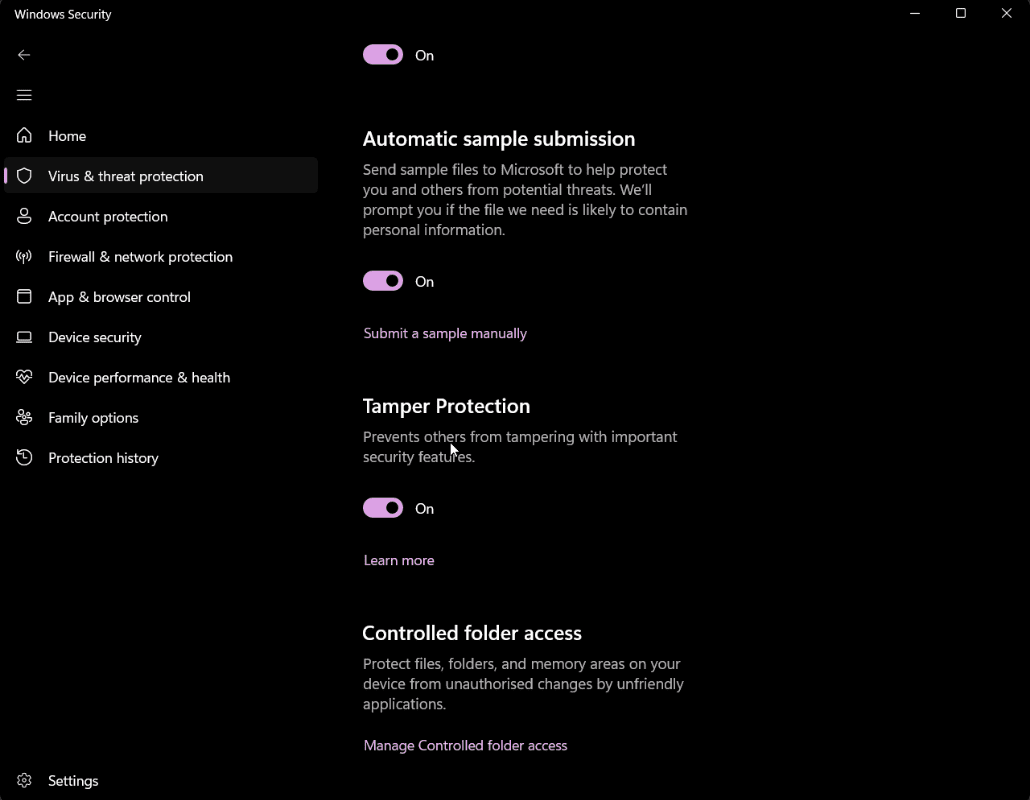
- Once that’s done, confirm Tamper Protection is enabled to stop malware from changing your settings. In the same menu, turn on Cloud-delivered protection and Automatic sample submission for up-to-date detections.
macOS (Ventura, Sonoma, and later)
Apple provides built-in background protections: Gatekeeper blocks untrusted apps, and XProtect blocks known malware. However, macOS doesn’t include a manual “scan entire system” option in System Settings.
If symptoms persist, install a reputable third-party antivirus tool and run a full system scan.
Restart in Safe Mode and check startup processes
Safe Mode loads only the essential drivers and services. If malware symptoms vanish in Safe Mode but return during a normal boot, that strongly suggests a third-party program is involved.
Windows 11
- Hold Shift and click Restart from the Start menu. Select Troubleshoot > Advanced options > Startup Settings > Restart. You can then press 4 or F4 for Safe Mode or 5 or F5 for Safe Mode with Networking. The networking option includes internet access, which can be useful if you need to download updates or tools while troubleshooting.
- After login, open Task Manager > Startup, and disable entries you don’t recognize.
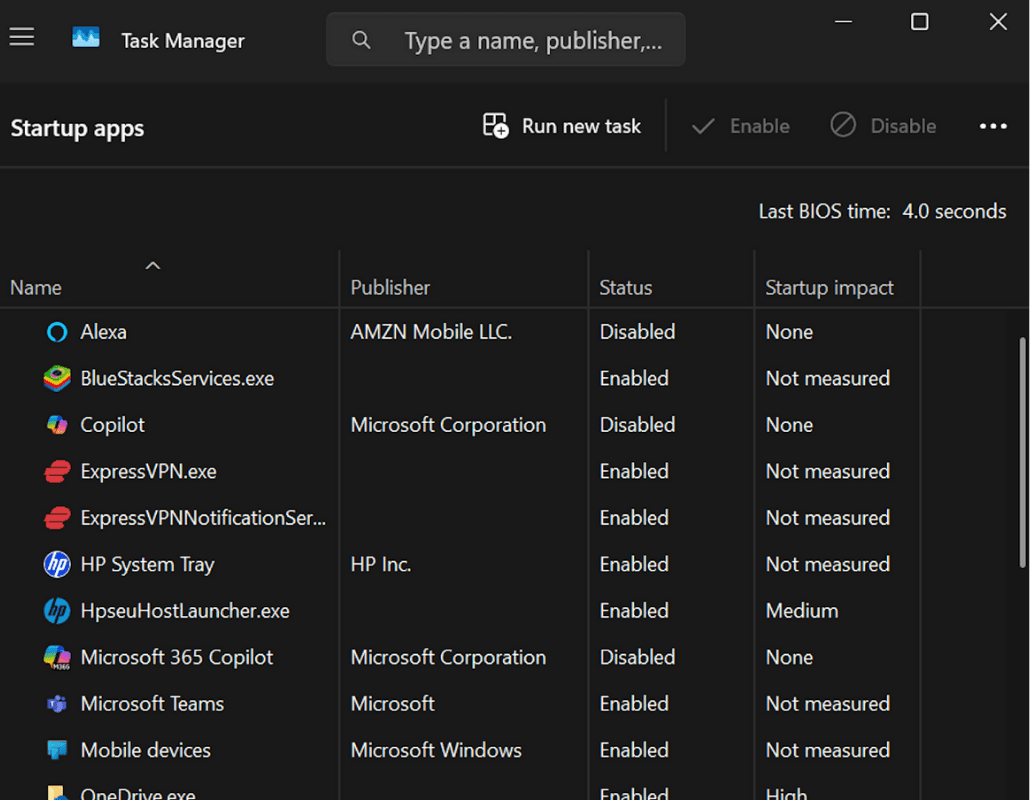
- Then, open Task Scheduler and look for tasks with unusual triggers or actions. For example, a suspicious task might be set to run every few minutes without reason or point to an unfamiliar .exe stored in AppData instead of a standard Windows folder.
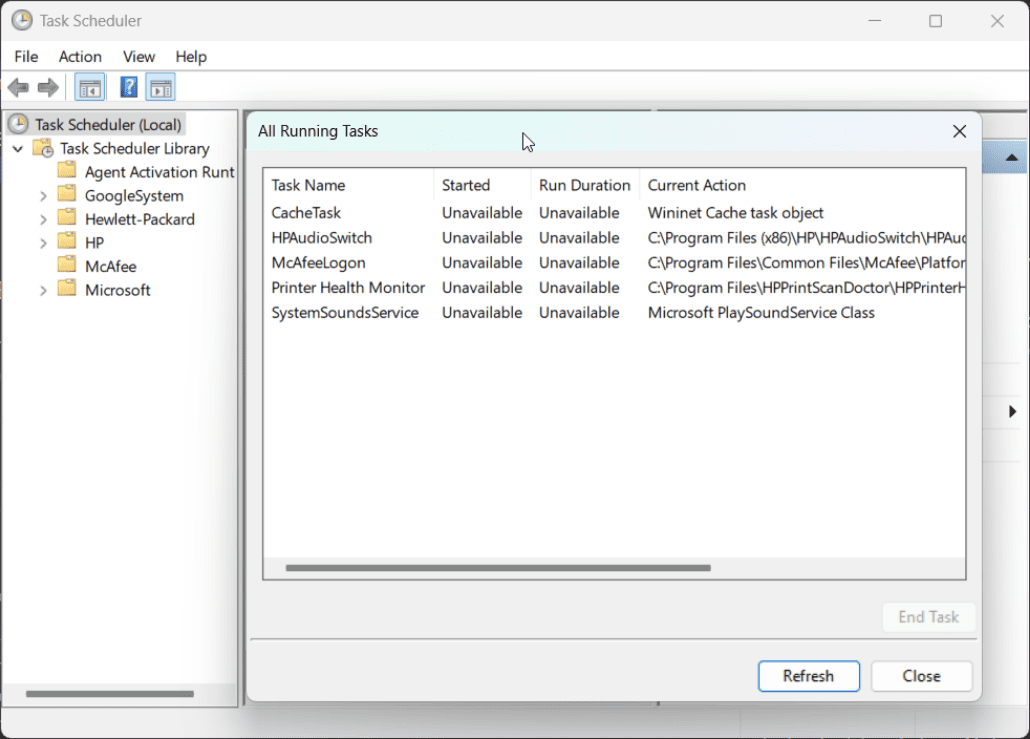
- If you find a suspicious task, check the Action field to see what program or file it launches. If it’s linked to an installed application, go to Settings > Apps > Installed apps, sort by Install date, and uninstall the program. Note the file paths before removal so you can confirm the associated files are gone.
 If the task points to a standalone file (for example, an .exe or script in AppData or ProgramData) that doesn’t appear in Installed apps, manually delete or quarantine that file instead.
If the task points to a standalone file (for example, an .exe or script in AppData or ProgramData) that doesn’t appear in Installed apps, manually delete or quarantine that file instead.
macOS
- On Apple Silicon, shut down, hold the power button until Loading startup options appears, select your disk, and hold Shift. Then, click Continue in Safe Mode. On Intel Macs, restart while holding Shift.
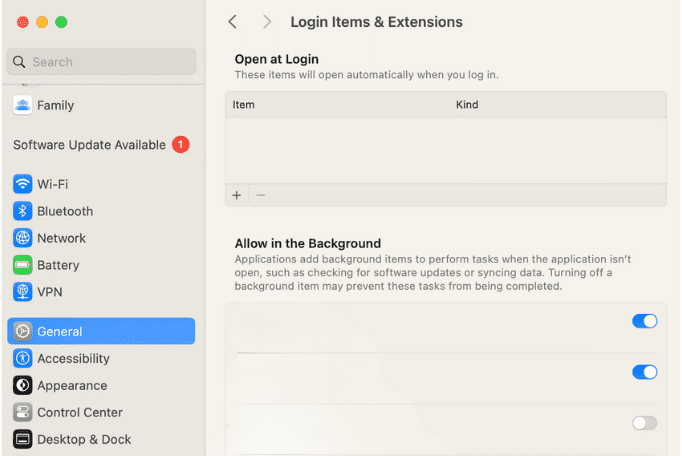
- After login, go to System Settings > General > Login Items and Extensions and remove any unfamiliar entries. At the top, you can remove apps set to open at login, and further down, you can toggle background items on or off. Double-check unfamiliar entries before disabling them, since some may be needed for legitimate apps.
- Inspect the /Library/LaunchAgents and /Library/LaunchDaemons folders, as well as the equivalents inside your user folder (~/Library/LaunchAgents). To reach them, open Finder, press Command + Shift + G, and type the path (for example, /Library/LaunchAgents).
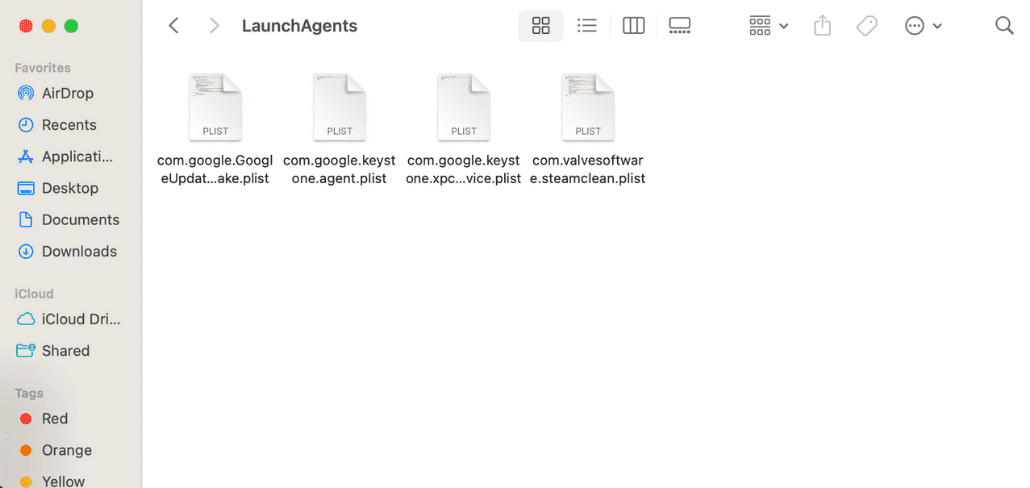
- Delete confirmed malicious items, empty the trash, and record their names so you can check for any traces left behind later.
Note: You should only disable or remove items you’re certain are malicious. Legitimate services can also appear unfamiliar, so when in doubt, research the entry before deleting it.
Delete suspicious files manually (if safe to do so)
You can try deleting malware files yourself, but this can be risky. Removing the wrong file can cause certain programs (or the system) to stop working. In some cases, malware can also come back if all its parts aren’t removed. If you're not confident, skip to using antivirus software. If you do delete files manually, back up important data and be ready to restore the system from a clean backup if something goes wrong.
After removing confirmed malicious files, clear temporary folders and caches to eliminate installers and scripts that could relaunch them:
- Windows: Go to Settings > System > Storage > Temporary files, then remove temp data and browser caches.
- macOS: Empty the trash, clear browser caches, and delete leftover installer files.
Download and install legitimate antivirus software
If built-in tools don’t resolve the issue (or you choose to skip the manual process), use a trusted antivirus program that offers real-time protection, which continuously monitors your system for suspicious activity. Download the software directly from the official vendor’s website to avoid tampered or fake versions.
Once installed, run a full system scan, which examines all files and programs on your computer for known malware patterns or unusual behavior. The antivirus will then quarantine or block any threats it finds, isolating them so they can’t harm your system.
Restore your system from a clean backup (if infection persists)
Restoring from a known-clean backup is often faster and safer than hunting down persistent fragments.
Windows
- System Restore: From the Control Panel, select Recovery > Open System Restore. Choose a restore point dated before the problem began. Note that System Restore must have been enabled previously; otherwise, no restore points (snapshots of your configuration and settings at a specific moment) will be available. This rolls back system files and settings but doesn’t affect personal documents.
- Full-disk image: If you previously created a full-disk backup using tools like Windows Backup or third-party imaging software, follow the program’s instructions to restore the image. After restoring, install the latest updates before reconnecting to the internet.
macOS
- Time Machine: Connect your external drive or access your network backup. Open Time Machine from the Applications folder or menu bar, then browse snapshots taken when your system was healthy. Verify the backup date and restore only the files or system state you need.
Reset or reinstall the operating system as a last resort
When all else fails, restoring your system to a known-good baseline guarantees removal of software-level threats. This should only be attempted after backups and other cleanup methods have failed.
Windows 11
Use Settings > System > Recovery > Reset this PC. Choose Remove everything for a full wipe. Then, select Cloud download (downloads the latest system version) or Local reinstall (faster, uses local files).
macOS
On your Mac, go to System Settings > General > Transfer or Reset > Erase All Content and Settings. If you’re using an older device, use Recovery to erase and reinstall macOS via Disk Utility.
Important: This wipes all user data, apps, and settings, so it’s best to back everything up before proceeding.
Update your system after cleaning
After your device is stable, install all pending updates for your operating system, drivers, and applications. Keeping everything up to date helps close security gaps that malware can exploit. If you don’t mind occasional restarts, turn on automatic updates so you stay protected without thinking about it. If you prefer to avoid restarts, set a regular manual schedule for checking and installing updates, and stick to it consistently.
Change your passwords after removing the virus
If your computer may have been infected with keyloggers or browser hijackers, or if you’ve received suspicious account alerts, assume your passwords could be compromised. On a device you know is clean, update your passwords for email, banking, cloud storage, and other important accounts. Use strong, unique passwords for each account and enable two-factor authentication (2FA) wherever possible for extra protection.
How to prevent future infections
Keep your operating system and apps updated
Apply patches to your operating system, browsers, drivers, and office suites on a consistent schedule. For most users, automatic updates provide the best protection and should be left enabled.
If you prefer to manage updates manually, review them on a regular basis. Prioritize software that faces the internet: browsers, email clients, messaging apps, and anything that opens file attachments. Many malware families exploit vulnerabilities that were fixed months earlier, making routine patching one of the most effective defenses.
Avoid downloading files from unknown sources
Download software only from publishers or trusted app stores. Avoid repacks, cracks, and key generators, as they frequently bundle hidden malware. If a website insists you install a “codec,” “update,” or “player” before viewing content, leave immediately; legitimate sites typically don’t require random helper software for common formats.
Don’t click on suspicious links or ads
Treat urgency and scare tactics as red flags, and hover over links to preview the true destination before clicking. Close pop-ups using your browser’s controls rather than buttons inside the pop-up itself. Modern browsers and email clients (including Chrome, Edge, Safari, and Gmail) include built-in phishing protection, so make sure it remains enabled in your settings.
ExpressVPN’s Threat Manager can block known trackers and malicious domains at the network level, reducing the chance of landing on harmful sites in the first place.
Use a password manager and 2FA
Reused passwords can allow one breach to compromise multiple accounts. A password manager like ExpressKeys creates and stores strong, unique passwords for each login and makes changing passwords easier after an incident. Enable two-factor authentication (2FA) on important accounts. ExpressKeys also generates and stores 2FA codes, so you don’t need a separate authenticator app.
Where possible, choose app-based verification codes over SMS verification. These are safer because texts can be redirected if someone convinces your phone carrier to move your number to another SIM card.
Learn how to identify phishing attempts
Phishing remains the leading way that malware spreads and accounts are hijacked. You should verify the sender’s identity through a separate, official channel (such as a service provider’s customer support page) if a message asks you to act quickly. Look for telltale signs such as spelling errors, mismatched domains, or attachments that don’t fit the context. For common warning signs, see our guide to phishing email red flags.
Use a virtual private network (VPN) on public Wi-Fi
Public Wi-Fi networks can be misconfigured, unencrypted, or even intentionally set up by attackers as rogue hotspots. On these networks, nearby users could potentially intercept unprotected traffic, redirect you to fake login pages, or inject malicious content. A VPN encrypts your connection, making it much harder for anyone on the same network to eavesdrop, tamper with your data, or track your activity.
While a VPN protects your data in transit, it’s not a substitute for antivirus or endpoint security. Use it alongside security software, especially when signing into accounts, transferring files, or accessing sensitive resources on shared networks such as cafés, airports, or hotels.
FAQ: Common questions about computer viruses
Can a virus infect your computer without you knowing?
Yes. Many virus variants are designed to hide, running in the background while stealing data, logging keystrokes, or spreading across networks without obvious signs.
What’s the difference between malware and a virus?
Malware is a broad term for any software designed to harm, exploit, or take control of a computer, including spyware, ransomware, trojans, worms, and viruses. A virus is a specific type of malware that spreads by attaching itself to files or programs, often requiring user action to propagate.
Can Mac computers get viruses too?
Yes. While macOS includes built-in protections, Macs can still be infected by malware delivered through malicious apps, browser hijackers, or phishing downloads. No system is completely immune, so practicing safe browsing and keeping software up to date is important.
Do all computer viruses show visible symptoms?
No. Some cause crashes, pop-ups, or slow performance, but many operate quietly to steal information or disable defenses. Lack of symptoms doesn’t mean the system is clean, which is why real-time malware protection is important.
Is formatting your computer always necessary to remove a virus?
No. Most malware can be removed with antivirus tools, Safe Mode cleanup, or restoring from backups. Reinstalling or formatting is only needed when the infection resists other methods or has deeply damaged system files.
What is the most common computer virus today?
There isn’t one single dominant virus. The most common malware families include trojans, which hide inside seemingly legitimate apps; ransomware, which locks files for payment; worms, which spread across networks; and adware, which bombards devices with unwanted ads.
How can I prevent a computer virus?
The best defense is a combination of good habits and tools. Keep your system and apps up to date, only download files from trusted sources, and watch out for suspicious email links or attachments. Run a reliable antivirus with real-time protection, use strong, unique passwords with two-factor authentication (2FA), and consider a virtual private network (VPN) on public Wi-Fi to keep your connection secure. Staying aware of phishing attempts and unusual messages can prevent most infections before they even start.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN