ExpressVPN-Blog
Privatsphäre, Cybersicherheit und Neuigkeiten zum Thema VPN

Letzte Beiträge
Alle anschauen-

eBay-Betrug vermeiden: Kompletter Leitfaden für Käufer und Verkäufer
eBay bietet nahezu alles, was du suchst, von Sammlerstücken über Elektronik bis hin zu Gebrauchtwagen. Wie jede große Plattform zieht aber auch eBay Personen an, die Käufer oder Verkäufer täusch...
-

Wo deaktivieren Mein iPhone suchen: Schritt-für-Schritt-Anleitung
Das Deaktivieren von „Wo ist? Mein iPhone“ ist Teil der Vorbereitung, um das Eigentum eines Geräts zu übertragen, beim Wechsel der Apple-ID oder bei der Einsendung zur Reparatur. Die Funktion is...
-

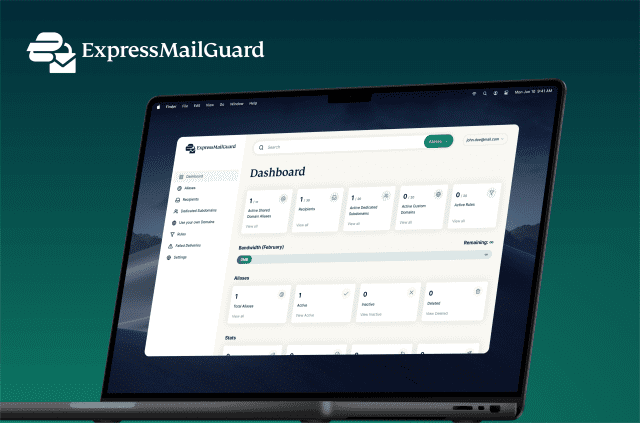
E-Mail-Sicherheit verbessern: Schritt-für-Schritt-Anleitung
Dein E-Mail-Konto ist einer der wichtigsten Zugänge zu deinem gesamten Online-Leben. Viele Dienste nutzen es als primären Wiederherstellungsweg. Wer Zugriff auf dein Postfach hat, kann Passwortzurü...
ExpressVPN News
Alle anschauenEmpfohlenes Video
-

Die 10 besten Videospiele, die Ihre Meinung zum Thema Datenschutz ändern werden
https://www.youtube.com/watch?v=7uOfHGT5p4w Wenn Sie Online-Gaming lieben und am Thema Datenschutz interessiert sind, sollten Sie diese Videospiele ausprobieren, bei denen es um Hacker, Cybersi...