SSH vs. VPN: Which should you use?
Whenever you connect to the internet, there’s a risk that your data could be exposed. To maintain privacy, many people turn to tools that protect their traffic. Two common options are setting up Secure Shell (SSH) or connecting through a virtual private network (VPN). Both use encryption and create secure data tunnels, but otherwise function differently.
In this guide, we’ll explain what each one does, how they protect your data, and when it makes sense to use one or the other.
SSH vs. VPN: What’s the difference?
SSH and VPNs are both tools you can use to protect your traffic, but they work differently and have distinct use cases.
SSH is usually used to connect to another computer in order to do things like move files or run commands from afar. It’s often employed by people who manage servers. SSH keeps the connection encrypted but requires configuration. Rather than covering your entire device, each SSH will only secure a specific app’s connection. And if you need to encrypt connections from more than one source, you’ll need multiple SSHs.
VPNs, on the other hand, usually cover everything. Once you turn one on, all the internet traffic from your device goes through a secure tunnel. Using one will also hide your IP address, so websites and services see the VPN server’s location rather than yours.
While both provide encryption and enhanced privacy, they solve different problems. Using SSH is more focused and hands-on. VPNs are much easier to use and provide broader protection, offering a fully encrypted connection with just a few clicks.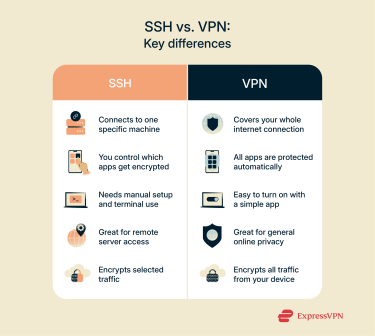
What is SSH?
SSH is a way to securely connect to another computer over the internet. It’s a handy way to manage servers or work on a device that’s not physically in front of you.
The key is that SSH keeps everything private. When you type a command or send a file, SSH encrypts that data before it leaves your computer. So even if someone is watching the network, they won’t be able to see what you’re doing.
In short, SSH primarily offers a secure way to remotely access another machine.
How does SSH work?
At its core, SSH sets up an encrypted connection between your device and a remote machine. In simple terms, here’s how it works:
- Your device and the server exchange cryptographic keys. Each one has a public and a private key.
- The server checks your identity by comparing the key you’re using with the one it knows.
- If everything matches, the two sides agree on a shared key that encrypts the rest of the session.
This process is based on something called public key cryptography. It keeps outsiders from reading the traffic, even if they manage to intercept it.
SSH typically runs on port 22 and uses Transmission Control Protocol (TCP), which helps make it so all data packets arrive correctly and in the right order. You can also log in using a password, but using SSH keys is more secure and preferred under most circumstances.
What is an SSH tunnel?
An SSH tunnel is a secure way to pass data through your SSH connection. Instead of sending traffic directly to a destination, you route it through the tunnel, and SSH carries it the rest of the way.
This is especially useful when:
- You need to access something inside a private network.
- You want to access a blocked service and are looking for a safe way to bypass the restriction.
- You want to protect traffic from a specific app or program without using a VPN.
Tunneling works through port forwarding, which simply means taking traffic meant for one place and quietly passing it along to another. SSH listens on a local port, wraps the traffic, and forwards it to a target machine, even if it’s behind a firewall.
In some cases, you can also set up a SOCKS proxy through SSH. That lets you point your browser or another app to the proxy, and all your web traffic will go through the SSH tunnel. From the outside, it looks like the traffic is coming from the SSH server, not from you.
What is a VPN?
A VPN forms a secure, encrypted connection between your device and the internet. When you use a VPN, your internet traffic is sent through a private tunnel to a server run by the VPN provider. From there, it goes on to the websites or apps you want to access. This process hides your real IP address, protects your data from being seen by others, and helps you stay more private online.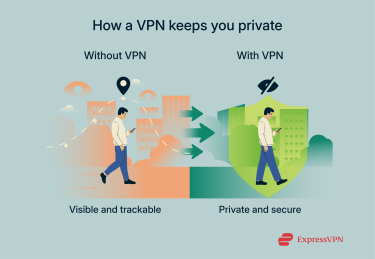 Unlike other tools that require technical setup or configuration, using a VPN can be as simple as flicking an on/off switch. You install the app, pick a server, and click to connect.
Unlike other tools that require technical setup or configuration, using a VPN can be as simple as flicking an on/off switch. You install the app, pick a server, and click to connect.
That connection creates an encrypted layer of privacy between you and the wider internet, which is especially useful if you're on public Wi-Fi or want to change your virtual location to access blocked content.
ExpressVPN does this by routing your traffic through secure, high-speed servers in various locations. It uses strong encryption and a no-logs policy to help keep your data private. Once connected, your traffic goes through ExpressVPN’s servers instead of your internet service provider (ISP), making it harder for others to see what you’re doing online.
With a VPN, you can protect your data, stop trackers, and browse more freely without having to worry about mastering the technical details of SSH.
How does a VPN work?
When you use a VPN, your device connects to a remote server run by the VPN provider. This server acts as a middle point between you and the wider internet.
Here's what happens behind the scenes:
- Your VPN app creates an encrypted tunnel between your device and the server.
- Everything you send, whether it’s data about the websites you visit, a message, or a file, is encrypted before it leaves your device.
- The VPN server decrypts that data and sends it to its final destination (like a website).
- The data you receive travels through the same encrypted tunnel.
The encryption means that even if someone intercepts your data, they won’t be able to read it. And because your real IP address is hidden, websites and services only see the IP of the VPN server, masking your actual physical location.
ExpressVPN uses industry-standard encryption and advanced security protocols to make this process fast and safe, no matter where you are.
What is a VPN tunnel?
The VPN tunnel is what makes everything private. It’s a secure path that wraps your internet traffic in layers of encryption, so nobody else can look inside.
You can think of it like this:
- Without a VPN, your data travels like a postcard: anyone along the way can read it.
- With a VPN tunnel, it’s more like a sealed envelope: only the sender and the receiver know what’s inside.
This tunnel also protects you on less secure networks, like public Wi-Fi. If you’re connected to a coffee shop’s Wi-Fi, for example, the VPN tunnel stops anyone else on that network from snooping on what you’re doing.
ExpressVPN keeps this tunnel stable and encrypted, even if your connection changes from Wi-Fi to mobile data. If the VPN drops for any reason, its Internet Kill Switch feature blocks all internet traffic until the connection is back, so your data stays protected.
While VPNs are designed to encrypt all data by default, some (like ExpressVPN) offer split tunneling, which lets you send only certain app or program traffic through the VPN (for example, only traffic from streaming apps).
SSH VPN: Can SSH replace a VPN?
SSH and VPNs are often compared because both can create encrypted tunnels and help route traffic securely. That’s why some users talk about setting up an “SSH VPN.” Essentially, this refers to using SSH tunneling to pass traffic through a remote server.
But while the idea might sound similar, the tools are built for different purposes. SSH can be configured to forward traffic, but this usually covers just a single application or port and requires some technical setup.
VPNs, on the other hand, are designed to encrypt and reroute all of your internet traffic automatically. The option to do split tunneling and only encrypt traffic from specific apps aside, VPNs cover your entire device. VPNs are also much easier to use.
So while SSH tunneling might be useful in some scenarios, it doesn’t offer the same level of coverage or the simplicity of a VPN.
Key differences in functionality
SSH and VPNs both use encryption and secure tunnels, but they’re built for different things.
- SSH is mostly for secure access to a specific machine. It can forward traffic, but usually one service or port at a time, and you have to set it up manually.
- VPNs generally cover your entire device. Once connected, all your traffic goes through an encrypted tunnel.
They also work at different levels:
- Because VPNs run at the network layer, they can reroute everything, almost like placing your device inside a private network. They typically use protocols like OpenVPN or Internet Key Exchange version 2 (IKEv2), but in many cases, organizations rely on Secure Sockets Layer (SSL) VPNs for secure remote access.
- SSH works at the application layer, meaning it only forwards what you tell it to and nothing more.
When using SSH as a VPN makes sense
Setting up a VPN is usually the go-to option for online privacy. But there are times when SSH tunneling may be a more practical choice.
For example, imagine you’re working from home and need to connect to a database that normally only accepts connections from inside your office network. Instead of installing a VPN, you can use SSH tunneling to securely route that connection through a server you control. In this case, SSH acts as a secure bridge, allowing just the traffic you need, nothing more. Here’s when SSH tunneling might make more sense than setting up a VPN:
Here’s when SSH tunneling might make more sense than setting up a VPN:
- You only need to access a specific service, like a database or internal tool.
- You’re comfortable using the command line and configuring SSH keys.
- You want to avoid setting up or maintaining a full VPN server.
- You don’t need to encrypt all your traffic, just one connection.
In these cases, SSH gives you flexibility without overcomplicating things. It’s not a full replacement for a VPN, but it works well when you just need secure access to one part of a system.
Limitations of SSH compared to VPNs
SSH tunneling is great for securing access to a specific service, but it does come with some limitations. Here are some of the key things to know:
- Only data sent through the forwarded port is encrypted.
- Multiple SSH tunnels need to be maintained to encrypt traffic from different apps.
- Your IP address remains unchanged, so you can’t browse the internet as if you were elsewhere.
- Setting up SSH tunnels requires technical skill.
Is SSH or VPN more secure?
In terms of encryption, both SSH and VPN use strong protocols to keep your data safe. The difference is more about what they protect than how well they do it.
SSH is designed to secure a single connection. It’s focused, great for remote access, and gives you more control for those who know how to use it. But it’s more limited in scope, protecting only specific connections rather than your entire device.
A VPN, in contrast, encrypts all internet traffic passing through your device. Unless you choose to only encrypt certain apps, every connection will be protected by default. This makes VPNs more practical for most users, especially those who aren’t comfortable using the command line.
When to use SSH and when to use VPN
SSH and VPNs solve different problems. It isn’t really a question of which tool is better; it depends on what you’re trying to do. Here’s a quick way to think about it:
- Use SSH when you only need secure access to one thing and you’re comfortable setting it up yourself.
- Use a VPN when you want to protect everything you do online with just a few clicks.
Pros and cons of SSH
SSH offers a secure and flexible way to access remote servers, but the level of protection and usability you get depends entirely on how it’s configured. From basic passwords to advanced certificate-based access, each method has its trade-offs.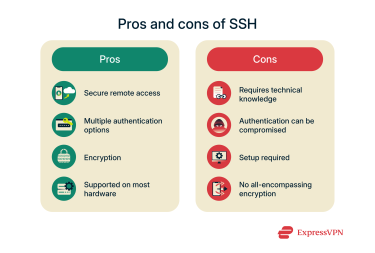
Advantages of using SSH
- Remote management: SSH enables users to securely connect to devices from afar. If you’re familiar with the command line, you can do all kinds of tasks remotely.
- Flexible authentication options: Choose whether to authenticate connections using passwords, keys, or certificates. Each offers a different mix of convenience and security.
- Data encryption: Multiple options exist for ensuring data sent over SSH is encrypted.
- Widely supported and accessible: Available on most operating systems and networking equipment, making it a standard tool for secure communication. Many tools that facilitate SSH are free and open source.
Limitations and risks of SSH
- Technical skills required: Setting up an SSH tunnel requires a degree of knowledge that many lack. The usual absence of a graphical interface can be tricky, and depending on what you want to use the SSH to do, you may need advanced knowledge of the command line.
- SSH keys can be stolen or leaked: If your private key ends up in the wrong hands, revoking it means tracking down every server where it’s been authorized. This is time-consuming and can be prone to error. You can opt for certificates instead, but these can be complex to set up.
- Requires proper configuration: Misconfigurations (e.g., permitting root login or weak ciphers) can undermine security, essentially defeating the purpose of the SSH.
- Limited scope: Each SSH will only encrypt a specific app or process, meaning SSH only offers limited security. You can run multiple at a time, but each SSH needs to be set up on its own.
Pros and cons of VPN
VPNs do a lot more than just hide your IP address. They’re versatile tools for improving online privacy and security, though it’s important to understand their limitations.
Benefits of using a VPN
- Hides your IP: Your real IP address and location get masked when you connect through a VPN. This can hide your real location.
- Encrypts your data: VPNs use strong encryption to protect your data as it travels across the internet. This can stop ISPs, advertisers, and websites from tracking what you do online.
- Helps avoid bandwidth throttling and other restrictions: Since your activity is hidden from your ISP, they’re less likely to slow down your speeds. Additionally, if your network administrator blocks certain content or types of connections, a VPN can offer a way around these restrictions.
- Lets you browse the internet as if you were in another country: By connecting to a server in another country, every website will treat your traffic as if it’s coming from that country.
- Shields you on public Wi-Fi: Public networks are often unsecured. A VPN keeps your connection private and safe from potential eavesdroppers.
- Blocks ads, trackers, and malicious sites (if included): Some VPNs come with features that block annoying ads, stop tracking scripts, and warn you about suspicious websites. Select ExpressVPN subscriptions also come with ExpressKeys, a password manager.
Drawbacks and potential issues with VPNs
Even with all the benefits, VPNs aren’t a perfect solution. Here are some drawbacks to keep in mind:
- Can slow down your connection: Encrypting your traffic and routing it through another server can affect speed. ExpressVPN helps keep this impact to a minimum with fast, modern protocols and smart server routing that avoids overcrowding.
- Not all VPNs are secure: Like any software, VPNs can have vulnerabilities; for example, older protocols like Point-to-Point Tunneling Protocol (PPTP) have well-known flaws, and issues such as TunnelCrack can allow traffic to leak outside the encrypted tunnel if misconfigured. ExpressVPN reduces these risks by supporting only secure protocols like Lightway, removing outdated protocols entirely, and implementing protections such as leak prevention technology and an automatic kill switch to help keep your data from escaping the encrypted tunnel.
- Subscription costs: Reliable VPNs typically require a paid subscription. While the cost is often modest, it’s still something to factor into your decision.
- May not work on all devices: While most phones and computers support VPN apps, some smart TVs and gaming consoles don’t. ExpressVPN works on a wide range of devices and also offers a dedicated VPN router to protect every device on your network.
- Doesn’t protect against everything: A VPN encrypts your traffic and hides your IP address, but it can’t stop you from voluntarily sharing personal information with websites like Google or Facebook. It also won’t prevent phishing attempts or block you from downloading malware, but to help reduce these risks, ExpressVPN includes Threat Manager, which uses a regularly updated block list to prevent your device from communicating with known trackers and malicious sites.
- Might be restricted in some countries: In a few places, VPNs are banned or heavily regulated. It’s always good to check local laws before using one.
SSH vs VPN: Which one is right for you?
It all comes down to what you’re trying to do. If you need to connect to a remote server, run commands, or transfer files in a secure way, SSH is a great option. It’s fast, encrypted, and ideal for system admins or developers who need direct access to a specific machine.
If your goal is to protect your internet traffic more generally, VPNs are a better choice. Using one will cover your entire device, so everything you do online goes through a secure, encrypted tunnel.
So:
- Go with SSH if you just need to securely access a remote system.
- Choose a VPN if you want greater privacy with regard to your internet traffic.
Both are useful, just for different things. Knowing when to use each one helps you stay secure without overcomplicating things.
FAQ: Common questions about using SSH and VPNs
Is SSH safer than a VPN?
Not exactly. It depends on what you're trying to protect. Secure Shell (SSH) is ideal if you need secure access to remote machines. Data is only encrypted for an individual app or process. VPNs, on the other hand, usually encrypt all your internet traffic, protecting your browsing, apps, and background services. If you only need to manage servers securely, SSH is enough. But if you want to protect all your online activity, a VPN makes much more sense.
Can you use SSH as a VPN?
You can use Secure Shell (SSH) tunneling to create an encrypted connection and route some traffic through it. This achieves a result similar to what you’d get with a VPN, but it’s not the same. VPNs are easier to set up for full-device protection and can handle all traffic. SSH requires manual configuration and usually only tunnels specific ports or apps.
Is SSH faster than a VPN?
In many cases, yes. Secure Shell (SSH) tends to be lighter because it doesn’t encrypt your entire internet traffic like a VPN does. That can make it faster, especially on slow networks. But again, it depends on how each is configured and what you’re using it for.
Is SSH over the internet secure?
Yes. Secure Shell (SSH) is designed to work securely over untrusted networks. It uses strong encryption and key-based authentication to prevent unauthorized access. As long as it’s properly configured and kept updated, it’s a very secure option.
Do I need a VPN if I’m using SSH?
That depends on what you need. Secure Shell (SSH) secures your connection to a specific server. A VPN secures everything you do online. If you're just logging into a remote machine, SSH alone might be fine. But if you're using public Wi-Fi, are looking to mask your IP, or want full-device encryption, a VPN offers broader protection.
Can SSH bypass VPN restrictions?
Not really. Secure Shell (SSH) traffic goes through the VPN tunnel if the VPN is active, so it doesn’t bypass it. That said, some VPNs let you exclude SSH from the tunnel using split tunneling, which is useful if you need your real IP for a specific connection. But SSH isn’t meant to get around VPN blocks.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN

















Comments
Well of course a VPN company is going to recommend a VPN over SSH, to do otherwise would be bad for business, so I wasn't expecting too much, in the opposite direction.