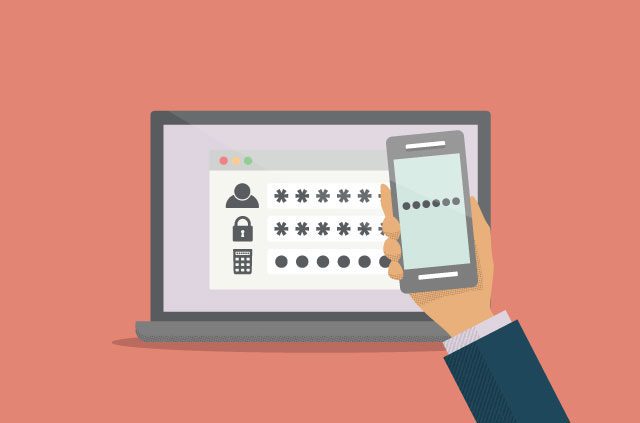
You might have skipped over your email provider’s prompt: Turn on two-factor authentication.
Two-factor authentication, or 2FA, is a secondary security measure for logging into an online account, whether it’s your banking service or a social media site. It means that after entering a username and a correct password, you are prompted to enter another piece of evidence to verify your identity. Often, this is a temporary code received by SMS on your mobile phone. Only after inputting this code will you be able to access your email.
But it’s not just SMS. With passwords being the first factor, the second factor in 2FA could be:
- Something you know: Personal identification numbers, answers to specific personal questions, keystroke patterns and other pieces of information that only you would know.
- Something you have: One-time passwords sent to your mobile phone, hardware token or other item in your possession; or generated codes in authenticator apps such as Google Authenticator and Authy.
- Something you are: Biometric patterns from fingerprints, retina scans and voice prints.
This extra step can seem like a hassle just to log in to your e-mail or Facebook—but the security benefits are well worth the inconvenience.
How easy is it to defeat a password?
While the traditional combination of a username and password can provide a basic level of security, it is not foolproof.
First off, many people use weak passwords. According to SplashData, a company that analyzes millions of leaked passwords, some of the most common ones used are “123456,” “123456789,” and “password.” Just by using the most popular passwords, hackers would be able to successfully log in to numerous accounts.
Then there’s the risk of your password being stolen in a company’s security breach. Your information could be compromised before you are able to reset your password.
In addition, users tend to use the same passwords across different accounts for convenience. If one password is revealed, a hacker could simply try the same password for the individual’s other accounts to steal even more information about them.
Complicated passwords that combine lowercase and uppercase letters, numbers, and symbols are harder to guess but still vulnerable. Hackers may carry out brute-force attacks, in which they use a computer to try hundreds of thousands of passwords per second. They may also engage in phishing by disguising themselves as trustworthy individuals or corporations in an attempt to extract log-in credentials.
Which methods of 2FA offer the most protection?
2FA is only effective if no one can obtain your second-factor information. This is where authentication methods vary.
Codes sent by SMS are the least secure 2FA method. Your phone could be stolen or cloned, or the message could be intercepted or redirected. Someone could see the code if you allow text messages to be displayed on your lock screen, or someone could remove your phone’s sim card and used it in another phone to receive the code.
Security questions offer a low level of security, because of how easy it is to uncover or guess personal information. One way around this is to use your security question as a second password: Instead of actually answering the question, enter an unrelated phrase. Just don’t forget what your answer is.
Authenticator apps are highly secure methods of 2FA. Once you’ve set up the app to generate random codes for a given site, you’ll be able to access a code just by opening the app. The only way for someone else to read the codes would be if they had your phone (or other device with the authenticator app installed) and could unlock it.
Biometrics, which cover fingerprint scans, voice recognition and retina scans, are considered highly secure. While it’s possible for someone to record your voice or steal your fingerprints, these are still very unlikely scenarios. The best part of biometrics is convenience—you always have them with you. The question is whether you trust companies to keep your biometric information safe. You can’t change your biometrics if they become compromised.
A universal security key is a small piece of hardware you purchase (for about 50 USD) and plug into your computer to use for 2FA across multiple accounts. They typically have USB-A, USB-C and NFC connections, while Google makes one that also offers Bluetooth. First set up your accounts to recognize your key. To log in, connect your security key to your device when prompted, then press a button. This is one of the most secure methods right now; the only risk is someone stealing your key.
What do I do now?
Many of us are guilty of ignoring 2FA recommendations. We strongly suggest that you start reviewing your online accounts, especially those with sensitive information, and set up 2FA if you haven’t already done so. SMS codes are popular, but authenticator apps are just as convenient and more secure.
If the online services you use do not offer 2FA, improve your passwords. If you would like extra security, you could opt for password managers or Diceware, both services that help you use long and random passwords with ease.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN