Guide to combat digital stalking and harassment



- Netflix's hard-hitting documentaries, Baby Reindeer and Can I Tell You A Secret?, underscore the urgent need for digital privacy awareness. Inspired by these haunting narratives, we've created a comprehensive guide to combat cyberstalking and harassment.
. - Cherlynn Cha, Security Operations Center Manager at ExpressVPN, lends her cybersecurity expertise, emphasizing protective measures like strong passwords and VPN use.
. - While cyberstalking and digital harassment are two different practices, they both aim to control and instill fear—using tactics like unsolicited messages, public shaming, and the creation of fake profiles.
. - 41% of U.S. adults have faced online harassment versus 51% of Brits. More than 20% of Americans have experienced cyberstalking, as have 25% of Britons, highlighting an urgent call for awareness and protective actions.
. - Strategies to combat digital abuse include setting strict privacy controls, alerting your network of friends, family, and colleagues if someone is impersonating you, and documenting interactions for potential legal actions.
. - Supporting victims involves offering a safe space, educating oneself and others, and advocating for stronger legal protections to tackle digital harassment effectively.
Ever felt a chill run down your spine while binge-watching Netflix? That’s the kind of unsettling buzz Baby Reindeer has stirred, with its gripping real-life narrative of physical and digital stalking. The series, based on comedian Richard Gadd’s harrowing experiences, throws a spotlight on the eerie reality of being watched both offline and online.
Similarly, Netflix’s Can I Tell You A Secret? delves even deeper into the unnerving world of cyberstalking and digital harassment. This documentary showcases the dark world of cyberstalking and digital harassment, highlighting the stories of three women—Zoe Jade Hallam, Lia Hambly, and Abby Furness—each ensnared in the web of online harassment from a single perpetrator.
Their harrowing experiences, from being impersonated to receiving relentless unwanted advances, serve as a stark reminder of the dark side of our digital interconnectedness. Social media and the internet, platforms designed to bring us closer, can also dangerously infringe upon our privacy.
In response to these victims' stories and the increasing concerns highlighted by both series, we’ve developed this guide with insights from Cherlynn Cha, a cybersecurity expert at ExpressVPN, offering practical steps for protecting yourself from digital abuse.
Ready to reclaim your digital peace of mind?
Disclaimer: This guide is for informational purposes only and does not offer legal or professional advice. If you’re facing threats or harassment, it’s important to consult with licensed professionals, such as legal advisors or law enforcement agencies. The strategies and information provided in this guide are intended to inform and guide and are not intended to replace expert advice in critical situations.
Jump to...
Understanding digital stalking and harassment
The psychological impact of online abuse
Digital stalking and harassment response guide
- Stage 1: Unwanted messages
- Stage 2: Social isolation
- Stage 3: Physical stalking and direct harassment
Protecting your online presence
How to support victims of digital stalking and harassment
A call for stronger safeguards
About the expert
Understanding digital stalking and harassment
Cyberstalking and digital harassment might sound like two sides of the same coin, but they play by different rules in our online world. Each has its own playbook for making life difficult, its own kind of havoc to wreak, and its own set of red flags. But at the heart of it, they share one sinister goal: to grab control and spread fear.
Here’s how they compare:
- Digital harassment typically involves repeated behavior intended to intimidate, control, or embarrass an individual. This can manifest through unsolicited messages, intimidation, public shaming, or spreading false information online.
- Cyberstalking, on the other hand, encompasses continuous monitoring, tracking, and unwanted communication. Stalkers may use spyware and GPS technology to track locations or create fake profiles to engage with or monitor their target.
| Digital harassment | Cyberstalking | |
| Definition | Involves repeated online behavior meant to intimidate, control, or embarrass an individual. | Involves continuous monitoring, tracking, and unwanted communication, creating a sense of fear and distress. |
| Methods | Unsolicited messages, public shaming or humiliation, spreading false information. | Use of spyware or GPS to track location, monitor online activity and communication, creating fake profiles to engage with the victim. |
| Impact | Leads to emotional distress, feeling unsafe online, and damage to reputation. | Causes significant fear for personal safety, leads to changes in daily routine, and affects mental health. |
| Signs | Receiving persistent, unwelcome messages; being the target of online rumors or defamation. | Feeling watched or followed online, noticing unfamiliar accounts showing excessive interest, unexplained knowledge of your personal life by others. |
41% of U.S. adults have experienced online harassment, with 20% having experienced digital stalking
The stories of Hallam, Hambly, and Furness in Can I Tell You A Secret aren’t isolated incidents but part of a larger, disturbing trend that spans globally. Studies and surveys consistently reveal alarming rates of digital harassment and stalking, highlighting the urgency for awareness and action.
Cha explains, “With the increasing use of social media and digital communication platforms, we have more people, and more information about people, on these platforms. The volume of digital harassment has increased as it’s become easier for stalkers to find victims and information about their victims.”
A Pew Research Center study found that as many as 4 in 10 internet users in the U.S. have experienced some form of online harassment, ranging from less severe instances such as name-calling to more invasive forms like stalking. Similarly, a Statista study revealed that 51% of Brits have faced cyberbullying, and 36% have been trolled online.
Meanwhile, a separate survey indicated that cyberstalking was reported by approximately 1 in 5 Americans, with 29% stating that they know someone who had been a victim of an internet crime. Additionally, according to Statista, 25% of Brits have reported being victims of cyberstalking.
And the impact of digital harassment and stalking isn’t evenly distributed—with young women facing the highest risk. The Pew survey indicates that 33% of women under the age of 35 have experienced online harassment (compared with 11% of men), with a significant portion (13%) of these encounters escalating into stalking and physical threats.

"All it might take [for an online stalker] to track you down could just be a single photo of you.”
Cha says that the anonymity provided by the internet, along with the ease of creating fake profiles and accessing personal information has only exacerbated the issue. “Additionally, advances in technology like AI image recognition may offer new and easier ways for stalkers to find and harass their victims—all it might take to track you down could just be a single photo of you,” she says.
The psychological impact of online abuse
The trauma inflicted by cyberstalking and digital harassment extends far beyond the immediate stress of unwanted interactions. According to experts, victims often grapple with long-term psychological effects that can profoundly alter their sense of safety, trust, and well-being.
Anxiety and fear
Constant exposure to harassment can create a state of hyper-vigilance, where victims are always on edge, anticipating the next attack. This can lead to anxiety disorders and panic attacks, significantly impairing daily functioning. A study by the American Psychology Association (APA) found that victims of cyberstalking report higher levels of anxiety compared to those not targeted.
Depression
The isolation that often comes with being a target of online abuse can spiral into depression. The APA also notes that victims of cyberbullying, a form of digital harassment, show higher incidences of depressive symptoms, including persistent sadness, loss of interest in activities, and feelings of worthlessness.
Sleep disturbances
The stress associated with digital stalking and harassment can disrupt sleep patterns, leading to insomnia or nightmares. Research published in the Journal of Psychiatric Research indicates that individuals experiencing cyber harassment are more likely to suffer from sleep disturbances, affecting their overall health and ability to cope with stress.
Post-Traumatic Stress Disorder (PTSD)
In severe cases, digital stalking can trigger symptoms akin to PTSD, such as flashbacks, severe anxiety, and uncontrollable thoughts about the harassment. A study in the journal JMIR Mental Health highlighted the prevalence of PTSD symptoms among victims of online harassment.
Impact on self-esteem and social relationships
The pervasive nature of online abuse can also erode self-esteem and create a sense of isolation. Victims might withdraw from social interactions, both online and offline, to avoid further harassment. Research suggests that individuals who’ve experienced online abuse report decreased trust in others and a reluctance to engage in future online interactions.
The psychological aftermath of cyberstalking and harassment is a loud, clear reminder that vigilance online is non-negotiable. Persistent, unwelcome messages or that eerie feeling you’re being watched are alarms calling for action.
If you're unwillingly being harassed online, here's how to stand your ground and protect yourself at every stage:
Digital stalking and harassment response guide
Inspired by the unnerving progression observed in Can I Tell You A Secret?, this guide delves into the multifaceted nature of digital abuse, where cyberstalking and harassment sometimes morph into online privacy threats, eventually culminating in physical stalking.
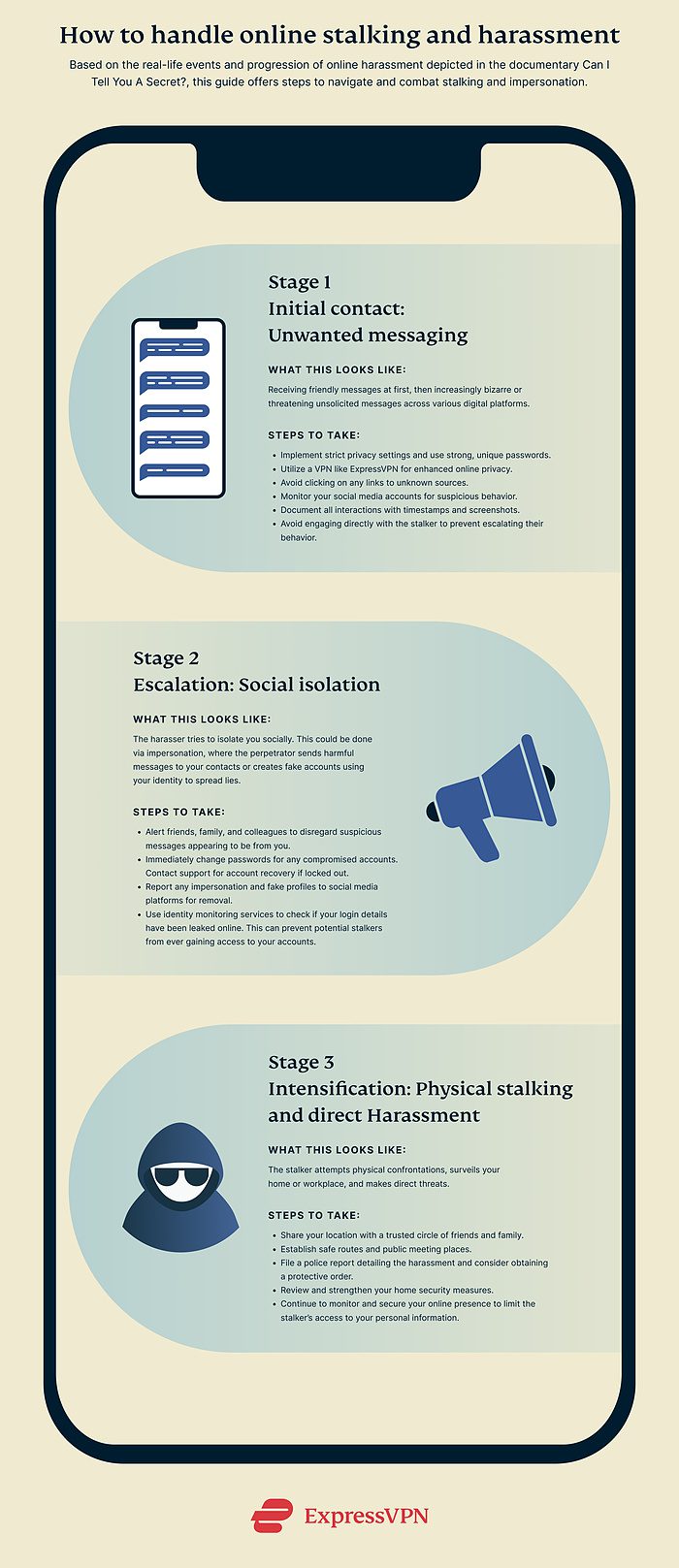
Stage 1: Initial contact—unwanted messaging
What it looks like
The journey into the nightmare of digital harassment often begins innocuously—an unknown person reaching out with a friendly message or two via one of your digital platforms. In the unsettling progression depicted in Can I Tell You A Secret?, victims first encounter messages that appear harmless, even sociable. However, the tone shifted quickly. The sender soon began to interject bizarre and discomforting messages, culminating in the ominous request: “Can I tell you a secret?”
Despite attempts to end the communication, the harassment intensified. Victims who blocked the perpetrator found themselves bombarded with messages from new accounts, enduring a relentless deluge of texts—sometimes receiving hundreds daily, ranging from nonsensical to outright threatening. This pattern indicates not just a breach of digital privacy but the onset of a targeted cyberstalking campaign.
Steps to take
“The moment you sense a breach in your digital space, it’s imperative to act,” says Cha. “Implementing strong privacy controls and using strong, unique passwords are your first line of defense.” Equally important is the documentation of all interactions. This serves not only as evidence but also as a clear record of unwelcome behavior if legal steps need to be taken.
Security measures
In response to the tactics employed by the show’s perpetrator—where friendly messages morph into a siege of harassment and attempts to hack the victims’ accounts—Cha recommends the following defensive strategies:
- Privacy and passwords: Shift social media profiles to private and employ strong, unique passwords across all accounts, leveraging a password manager for enhanced security. Activate two-factor authentication (2FA) to further obstruct unauthorized access attempts. Also, make sure you never share your one-time passwords (OTPs) with anyone.
- Use a VPN: Utilize a high-quality VPN like ExpressVPN to encrypt your internet connection and obscure your IP address, keeping your activity safe from interception and protecting your location from stalkers.
- Regular monitoring: Keep a close watch on social media activity for signs of unauthorized access or suspicious attempts to connect. Platforms typically alert users to unusual activity; heed these warnings and take immediate action.
- Dealing with persistent harassment: Given the perpetrator’s tactic of circumventing blocks by switching accounts, maintaining a heightened level of digital security is imperative. If you encounter messages baiting you with links, especially under the guise of revealing secrets or escalating contact, this could be an attempt to infiltrate your digital life further, possibly leading to account hacking as experienced by the victims in the documentary.
Documentation
Start keeping a meticulous record of all communications received from the stalker. This includes emails, direct messages, comments, and even attempts to contact you through others. Screenshots, timestamps, and saving copies of all interactions are essential as this documentation can serve as evidence should legal action become necessary.
Don’t engage
While the instinct might be to engage or confront, in cases of cyberstalking or harassment, silence can be more powerful. Engaging can sometimes fuel the stalker's motivations. Instead, focus on securing your digital footprint and seek support from friends, family, or professionals who can help navigate these turbulent waters.
Stage 2: Escalation—social isolation
What it looks like
During this stage, the harasser adopts a strategy designed to isolate the victims socially, employing tactics that usually blend psychological manipulation with criminal behavior. This could include hacking into victims’ social media accounts and impersonating them to send damaging messages to their friends, family, and acquaintances. For instance, in Can I Tell You A Secret?, one victim found her account being used to proposition a friend’s father for sex, while another was horrified to discover messages sent from her account to her friends’ husbands, ruining friendships and causing public humiliation.
And when the perpetrator was unable to hack directly into accounts, he created fake profiles bearing the victims’ names and photographs. These profiles were then used in a malicious campaign to defame and isolate the victims further, by contacting people close to them with inappropriate or misleading messages. This not only spread confusion and betrayal but also effectively turned the victims into social pariahs within their own networks, showcasing the perpetrator's calculated efforts to degrade and control their lives through digital means.
Steps to take
Immediate action
If a perpetrator has compromised or is attempting to compromise your accounts, Cha recommends the following:
- Alert your network: Inform friends, family, and colleagues about the harasser, advising them to disregard any suspicious or harmful messages received from what appears to be your account or from fake profiles mimicking your identity.
- Secure compromised accounts: If you still have access, immediately change passwords for any compromised accounts. If locked out, contact the platform's support team for account recovery or deactivation.
- Report impersonation: Report any fake profiles to the respective social media platforms. Most have protocols to handle impersonation swiftly and can work to remove fraudulent accounts.
- Enhance security measures: Update your security settings to further protect your accounts. This includes enabling 2FA, using strong, unique passwords, and reviewing app permissions.
Stage 3: Intensification—Physical stalking and direct harassment
What it looks like
This stage marks a transition from online harassment to tangible threats in the physical world. You might find that the stalker attempts to confront you in person, either by showing up unannounced at your home, workplace, or regular hangouts. Surveillance, like repeated drive-bys or finding evidence of someone lurking near your personal spaces, is a stark warning. Additionally, the nature of threats tends to become more direct, personal, and intimidating, indicating a severe escalation in the stalker's intentions.
For example, in Can I Tell You A Secret?, one of the perpetrator's earlier victims experienced a horrific year of torment. The stalker not only sent messages commenting on the color of her clothes while she was working at her car wash job, but also knew when she was alone in her vehicle, waiting while her boyfriend picked up a takeaway order. These invasive actions left her in a state of constant fear and hyper-vigilance, finding herself incessantly looking over her shoulder, searching for the stalker at every corner.
Steps to take
Cha highlights the need for a comprehensive approach to security that merges digital vigilance with physical safety measures. “At this point, your real-world identity has been compromised, and someone has found out who you are in real life. This requires an immediate and serious response,” she says.
Safety plans
If you believe you’re being stalked, it's essential for you to prioritize your physical safety. Share your live location with a close circle of trusted individuals who can keep tabs on your well-being. Establish safe routes for commuting and identify public places you can retreat to if you feel threatened. Changing your daily routine unpredictably can also throw off someone tracking your movements.
“Also review physical security measures, such as your home’s security,” says Cha. “If the stalker contacts you, do not engage, and especially do not meet them in real life.”
Legal recourse
“If you believe that your safety is at risk, report it to the police as soon as possible,” says Cha. File a police report detailing the harassment, including any evidence of online threats and attempts at physical encounters.
“Documentation from previous stages becomes invaluable here,” Cha adds. “Submit screenshots of the messages from the stalker and other related information such as their profile and username. For offline stalking, report any real-world interactions, including time and place.”
Seeking legal representation can also guide you through the process of obtaining protective orders, which are legal injunctions aimed at preventing the stalker from making any form of contact or approaching you.
Review your digital footprint
“Integrating digital and physical security measures is also essential,” advises Cha. “Continue to monitor and secure your online presence to prevent the stalker from gaining further information about you. Limit how much information you share about yourself online to mitigate the damage. For example, try googling yourself to see what information can be found about you publicly, and review your social media profiles and settings.”
Protecting your online presence
Cha says that stalkers use the information they can find online against their victims to harass them and compel them to engage. “While it might not be feasible or desirable to avoid putting information on social media at all, you can limit the exposure of your data.” Here’s how:
- Be cautious about sharing personal information online, such as your full name, address, phone number, or other identifying details. Limit the amount of information you share on social media and other online platforms, especially information that could help a stalker locate where you are.
- Take note of information that, while by itself doesn’t reveal your identity, could be used along with other pieces of information to reveal who you are.
- For example, your first name alone might not reveal much and neither does your place of work. However, if you put both your first name and the place you work in one account, these two pieces of information could be correlated to figure out exactly who you are.
- Review and update the privacy settings on your social media accounts and other online profiles. Many platforms give the option to customize access to the information you share—use them to limit who can see your posts, photos, and personal information.
- Avoid sharing your exact location and be cautious about sharing personal details that could be used to identify or locate you offline. Some social media platforms automatically tag your posts with your location—review those settings and turn this feature off if you don’t need it.
Check for leaked account credentials
While it's more common for cybercriminals to exploit data breaches, searching for login details on the dark web to hack into accounts, it's crucial to have a proactive defense strategy to prevent potential harm from a breached online account. Adopting a proactive defense strategy can help you prevent these incidents. Cha recommends using identity monitoring services to check if your email has been involved in any data breaches, potentially exposing login details. “My personal favorite is Have I Been Pwned, which keeps a huge database of past data breaches, and allows you to input your email to check if it has been previously compromised in any of those breaches,” she says.
If you discover your information is part of a data breach:
- Change your passwords immediately, especially for accounts using the same email or password exposed in the breach.
- Alert financial institutions if any financial information is at risk.
- Consider credit monitoring services to watch for unauthorized transactions or accounts opened in your name.
- Stay vigilant for phishing attempts that may use the breached information to trick you into giving away more data.
How to support victims of digital stalking and harassment
Knowing someone trapped in the shadows of digital stalking or harassment can leave you feeling helpless—but your support can be a beacon of hope. If you know someone who’s been stalked or harassed online or in person, here’s how you can help them reclaim their sense of safety and peace:
- Be their safe space: Start by listening. Open up a conversation where they feel seen and heard, without judgment. Validation can be incredibly powerful. Let them know it’s not their fault, they’re not alone, and that their feelings are completely valid.
- Educate yourself: Understanding the intricacies of digital stalking and harassment equips you to offer more than just emotional support—you become a valuable advisor. Familiarize yourself with the signs, the psychological impact, and the steps one can take to protect themselves.
- Guide them towards professional help: Encourage them to seek help from professionals, whether it’s legal advice, counseling, or cybersecurity experts. Navigating the aftermath of digital harassment can be overwhelming. Professional guidance can provide clarity, direction, and a sense of control.
- Resources and support: Compile a list of organizations, hotlines, and online resources dedicated to supporting stalking victims. Places like the National Cyber Security Alliance (NCSA) and The Cyber Helpline offer a wealth of information and assistance for those impacted.
- Advocate for their safety: Offer to help implement safety measures, from tightening up social media privacy settings to installing security software. Being proactive about safety can make all the difference. “It’s about creating a fortress around their digital life,” says Cha. “Simple steps like changing passwords, enabling 2FA, and educating about the importance of online privacy contribute significantly to their overall safety.”
- Stay present: Finally, keep checking in. Your continued support and reassurance can be a powerful force in their recovery journey.
A call for stronger safeguards
**Spoilers for Can I Tell You A Secret ahead**
Matthew Hardy, the central figure in Can I Tell You A Secret?, was sentenced to an unprecedented eight-year prison term for his invasive cyberstalking campaign. This landmark ruling underlines the severity of Hardy's exploitation of digital platforms to prey upon individuals like Hallam, Hambly, Furness, and many others. His conviction marks a critical juncture in combating digital stalking and harassment, spotlighting the need for a fortified digital infrastructure and the pressing necessity for legislative reform.
But this is only a starting point. Current laws lag behind the rapid evolution of digital capabilities, leaving gaping vulnerabilities that perpetrators like Hardy exploit. There's a need for laws better suited for the complexities of our online world—legislation that can effectively deter potential stalkers, provide clear recourse for victims, and outline specific, enforceable penalties for offenders.
Moreover, the role of law enforcement and judicial systems in enforcing these laws can’t be overstated. It's essential that these entities are equipped with the knowledge, tools, and resources to tackle cyberstalking head-on. This includes training programs that are up-to-date with the latest digital trends and cyber forensic techniques, ensuring effective response to reports of digital abuse.
However, until that shift occurs, awareness counts for a lot. Shows like Can I Tell You A Secret? not only expose dark truths but also underscore the power of knowledge. By spreading awareness, we directly confront the question the documentary poses with a resounding “no”.
About the expert
Cherlynn Cha is Security Operations Center Manager at ExpressVPN, where she plays a pivotal role in reinforcing the cybersecurity framework. With a focus on advanced threat modeling and threat hunting, Cha leads initiatives aimed at identifying and mitigating potential cyber threats. Her work is instrumental in ensuring the privacy and security of users by staying ahead of the evolving digital threats landscape. Through her expertise, Cha contributes to the development and implementation of robust security strategies, safeguarding users against the myriad risks present in the online world. Her commitment to privacy and security underscores ExpressVPN's mission to offer a safe, secure internet experience for all its users.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN