Expressvpn Glossary
Virtual private cloud
What is a virtual private cloud?
A virtual private cloud (VPC) is a logically isolated network segment within a public cloud environment. Organizations use VPCs to control IP address ranges, subnet configurations, and routing policies.
In many cloud platforms, a VPC provides tenant isolation even though multiple customers share the same underlying physical infrastructure. This isolation is implemented through software-defined networking, which lets administrators define network boundaries without deploying dedicated hardware.
How does a virtual private cloud work?
A VPC can be divided into public and private subnets and often works as follows: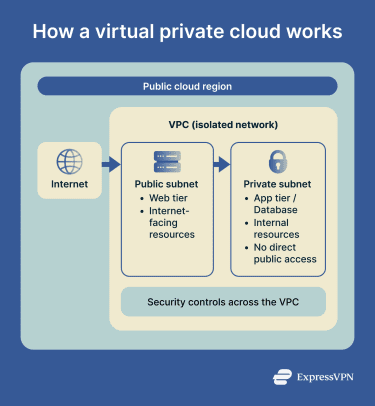
- Administrators define the VPC’s IP address range using a classless inter-domain routing (CIDR) block.
- In the public subnet, internet-facing resources such as load balancers or web tiers route traffic through an internet gateway. In Amazon Web Services (AWS), for example, a route table can send 0.0.0.0/0 to the internet gateway.
- In the private subnet, application and database tiers have no direct internet route. If outbound internet access is required, a Network Address Translation (NAT) gateway can let private-subnet resources initiate outbound IPv4 connections without accepting unsolicited inbound internet traffic. In AWS, a route table can send 0.0.0.0/0 to the NAT gateway. For outbound-only IPv6 access, AWS uses an egress-only internet gateway instead.
- Provider-managed firewall rules or security groups control allowed inbound and outbound traffic for workloads. In some cloud platforms, subnet-level controls such as network access control lists (NACLs) can also filter traffic at the subnet boundary. Identity and access management (IAM) policies control who can access and modify resources.
- Traffic visibility and private access complete the model. Flow-log features capture metadata on network traffic for monitoring, and private service access features, such as VPC endpoints or PrivateLink in AWS, can provide access to supported cloud services without sending traffic over the public internet.
Why is a virtual private cloud important?
VPCs strengthen network segmentation by isolating workloads into distinct logical zones. This architecture can reduce the attack surface by limiting which services are publicly accessible and by controlling traffic between workloads.
Many compliance frameworks require network-level controls and segmentation, and VPCs can help support those requirements. In regulated environments, they are often used as part of a broader control set for protecting sensitive data, rather than as a compliance requirement on their own.
Hybrid and multi-cloud strategies commonly use VPCs to connect on-premises networks with cloud environments. Organizations can extend or align existing network policies into the cloud while working toward more consistent security across locations.
Flow logs and inspection architectures can improve visibility into data flows and connection patterns across the environment.
Where is a virtual private cloud used?
Organizations use VPCs when they need secure, segmented networking for critical workloads. For example:
- Exposing web applications and APIs to the internet while keeping backend systems private.
- Isolating databases, caches, and internal services from direct internet access.
- Structuring microservices and multi-tier architectures with controlled communication between tiers.
- Connecting on-premises data centers to the cloud for hybrid deployments using site-to-site virtual private networks (VPNs) or dedicated links.
- Supporting compliance efforts in industries such as finance, healthcare, or government by enabling network segmentation and traffic controls.
- Supporting disaster recovery with standby or failover environments in a separate VPC, region, or other isolated cloud network environment.
Risks and privacy concerns
Misconfigured security group rules or overly permissive NACLs can expose private resources to unauthorized access. Administrators sometimes grant broader permissions than necessary, creating pathways to sensitive systems.
If attackers compromise a system, unrestricted outbound traffic can make it easier to exfiltrate stolen data from the network. Weak IAM controls can also grant attackers access to resources or management actions even when network defenses are in place.
Poor logging makes it difficult to detect and investigate incidents. Organizations that fail to monitor network traffic may miss warning signs until serious damage occurs. In addition, third-party access can increase risk if partners connect to systems without proper oversight or least-privilege controls.
Further reading
- Virtual private cloud (VPC): A detailed guide
- Security concerns in cloud computing and how to address them
- Zero-trust cloud security explained
- Ingress and egress: Everything you need to know
- IoT cloud security: Threats and best practices

